Securing Network Infrastructure: Discover practical network security with Nmap and Nessus 7
- تأليف
- دار النشر
- اللغة
- الإنجليزية
- الصيغة
- تصنيف
كتب واقعية
Plug the gaps in your network’s infrastructure with resilient network security models
Key Features:
Develop a cost-effective and end-to-end vulnerability management programExplore best practices for vulnerability scanning and risk assessmentUnderstand and implement network enumeration with Nessus and Network Mapper (Nmap)
Book Description:
Digitization drives technology today, which is why it’s so important for organizations to design security mechanisms for their network infrastructures. Analyzing vulnerabilities is one of the best ways to secure your network infrastructure.
This Learning Path begins by introducing you to the various concepts of network security assessment, workflows, and architectures. You will learn to employ open source tools to perform both active and passive network scanning and use these results to analyze and design a threat model for network security. With a firm understanding of the basics, you will then explore how to use Nessus and Nmap to scan your network for vulnerabilities and open ports and gain back door entry into a network. As you progress through the chapters, you will gain insights into how to carry out various key scanning tasks, including firewall detection, OS detection, and access management to detect vulnerabilities in your network.
By the end of this Learning Path, you will be familiar with the tools you need for network scanning and techniques for vulnerability scanning and network protection.
This Learning Path includes content from the following Packt books:
Network Scanning Cookbook by Sairam JettyNetwork Vulnerability Assessment by Sagar Rahalkar
What you will learn:
Explore various standards and frameworks for vulnerability assessments and penetration testingGain insight into vulnerability scoring and reportingDiscover the importance of patching and security hardeningDevelop metrics to measure the success of a vulnerability management programPerform configuration audits for various platforms using NessusWrite custom Nessus and Nmap scripts on your ownInstall and configure Nmap and Nessus in your network infrastructurePerform host discovery to identify network devices
Who this book is for:
This Learning Path is designed for security analysts, threat analysts, and security professionals responsible for developing a network threat model for an organization. Professionals who want to be part of a vulnerability management team and implement an end-to-end robust vulnerability management program will also find this Learning Path useful.
Sairam Jetty has more than 5 years of hands-on experience in many verticals of penetration testing, compliance, digital forensics, and malware research. He is currently working with Paladion Networks, Abu Dhabi, as a senior analyst and team lead. He has assisted and associated with various financial, telecom, and industrial institutions for testing and securing their applications and environments. Sairam has industry-standard certifications, such as OSCP, Digital Forensic Analyst, Digital Forensic Investigator, and Mobile Security Expert. He also specializes in source code review and mobile application security. He has acquired a great knowledge of SCADA/ICS and nuclear security from his corporate experience and self-learning. Sagar Rahalkar is a seasoned information security professional with an experience of 12 years in various verticals of IS. His domain expertise is in Cybercrime investigations, Forensics, AppSec, VA/PT, Compliance, IT GRC and so on. He has a master's degree in computer science and several certifications, including Cyber Crime Investigator, CEH, ECSA, ISO 27001 LA, IBM AppScan Certified, CISM, and PRINCE2. He has been associated with Indian law enforcement agencies for around 4 years for dealing with cybercrime investigations and related training. He has received several awards and appreciations from senior officials of the police and defense organizations in India. He has also been a reviewer and author for various books and online publications.
© 2019 Packt Publishing (كتاب إلكتروني): 9781838646974
تاريخ النشر
كتاب إلكتروني: 26 مارس 2019
واستمتع آخرون أيضًا...
- Smart Work: The Ultimate Handbook for Remote and Hybrid Teams Jo Owen
- Ultimate Cyberwarfare for Evasive Cyber Tactics Chang Tan
- The Organized Academic: How to Transform Your Academic Life Elizabeth A. Wells
- ADHD in Adult Life: How to Deal With Responsibilities Without Freaking Out MAX EDITORIAL
- Smart Leadership: The Ultimate Handbook for Great Leaders Jo Owen
- All The Work You Shouldn't Do: How to Succeed at University Ruby Cline
- A Country Doctor Sarah Orne Jewett
- PMP Pro: Transform Your Exam Success with Game-Changing Secrets: "Elevate your PMP exam results! Dive into transformative audio lessons for peak performance on test day." Arden Blakewood
- Desconexión Digital: Meditaciones Guiadas para Calma y Claridad Refeser
- Nature’s Symphony of Serene Forest Cricket Sounds Mixed With Piano Rhythms For Deep Calm & Relaxation: Experience Soothing Nights for Restful Sleep & Mindfulness Using Enhanced BGM 8D Audio Cedar Skye
- GED Secrets: Elevate Your Success and Conquer the Exam Today: "Boost your GED prep! Unlock engaging audio lessons for ultimate exam success today!" Ronan Cade
- Nature’s Symphony Of Soothing Lake Soundscapes For Meditation, Deep Relaxation & Stress Relief: Embrace The Harmony & Feel The Water Waves With Blissful 8d Audio For Inner Peace & Serenity Cedar Skye
- The Complete Falconer Files Brief Cases Books 1 - 8 Andrea Frazer
- For All Time: First in the Liza Marchant Series Marian L Jasper
- Data-Driven Decisions: Mastering Business Data Science Chuck Sherman
- Nature’s Symphony of Tranquil Forest Soundscapes Using Enhanced 8D Audio For A More Natural Relaxation: Meditation Aid For Unmatched Calm, Emotional Healing, Mental Clarity & Stress Relief Cedar Skye
- Notas sobre Enfermería: (Español latino) Florence Nightingale
- SHRM: Your HR Exam Success with Insider Secrets: "Boost your HR exam readiness! Harness powerful audio lessons packed with insider tips for ultimate success." Ronan Ashwood
- NONPARTICIPANT: A New Dawn Rob Johnson
- Intermediate Japanese: Broaden Your Japanese Vocabulary and Cultural Understanding Yuki Abe
- Ne, ne, ne, was hab ich bloß?: Humorvolle Geschichten über den menschlichen Körper Edla Pinnow
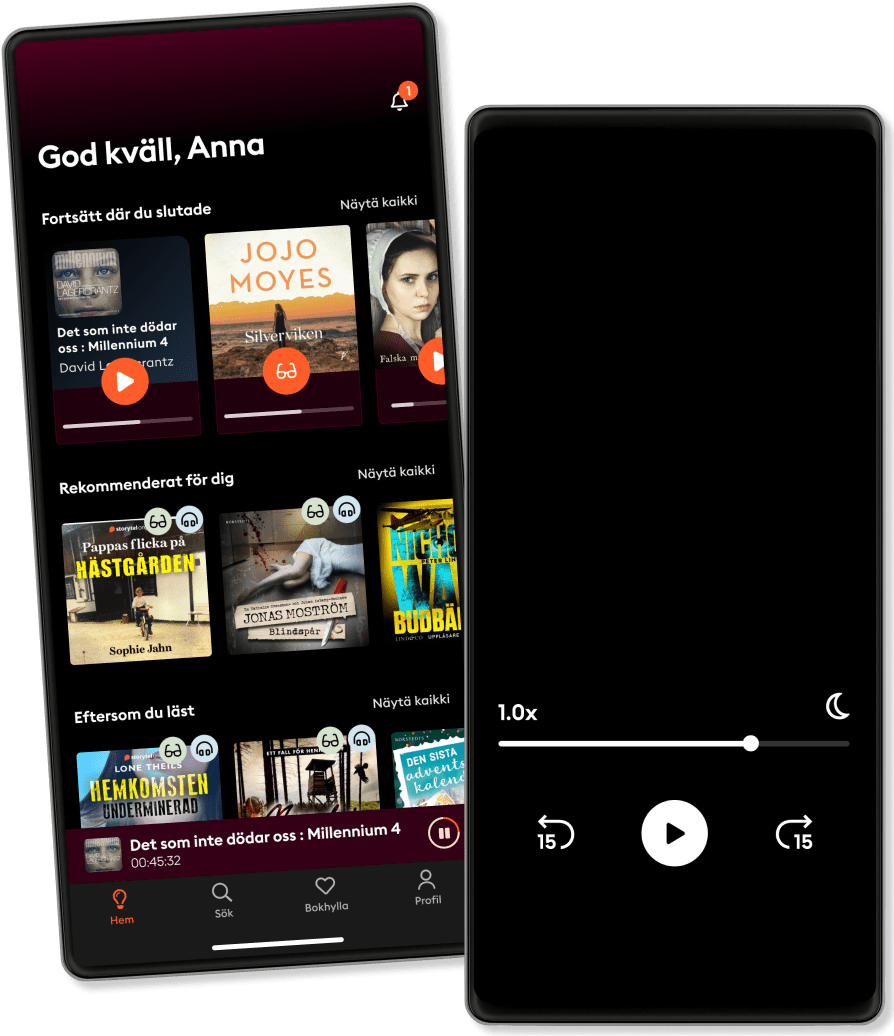
دائمًا برفقة Storytel
أكثر من 200000 عنوان
وضع الأطفال (بيئة آمنة للأطفال)
تنزيل الكتب للوصول إليها دون الاتصال بالإنترنت
الإلغاء في أي وقت