Managing Lateral Movement
- Por
- Episodio
- 129
- Publicado
- 26 ago 2021
- Editorial
- 0 Calificaciones
- 0
- Episodio
- 129 of 339
- Duración
- 29min
- Idioma
- Inglés
- Formato
- Categoría
- No ficción
All links and images for this episode can be found on CISO Series For four years in a row, Verizon's DBIR, has touted compromised credentials as the top cause of data breaches. That means bad people are getting in yet appearing to be legitimate users. What are these malignant users doing inside our network? What are the techniques to both understand and allow for good yet thwart bad lateral movement? Check out this post for the basis for our conversation on this week's episode which features me, David Spark (@dspark), producer of CISO Series, co-host Steve Zalewski, and our sponsored guest Sandy Wenzel (@malwaremama), cybersecurity transformation engineer, VMware. Thanks to our podcast sponsor, VMware In this episode: • Why are bad people getting inside our networks? • Can machine learning help find them? • How can we separate lateral movement from credential stuffing? • Would using threat modeling and going passwordless help?
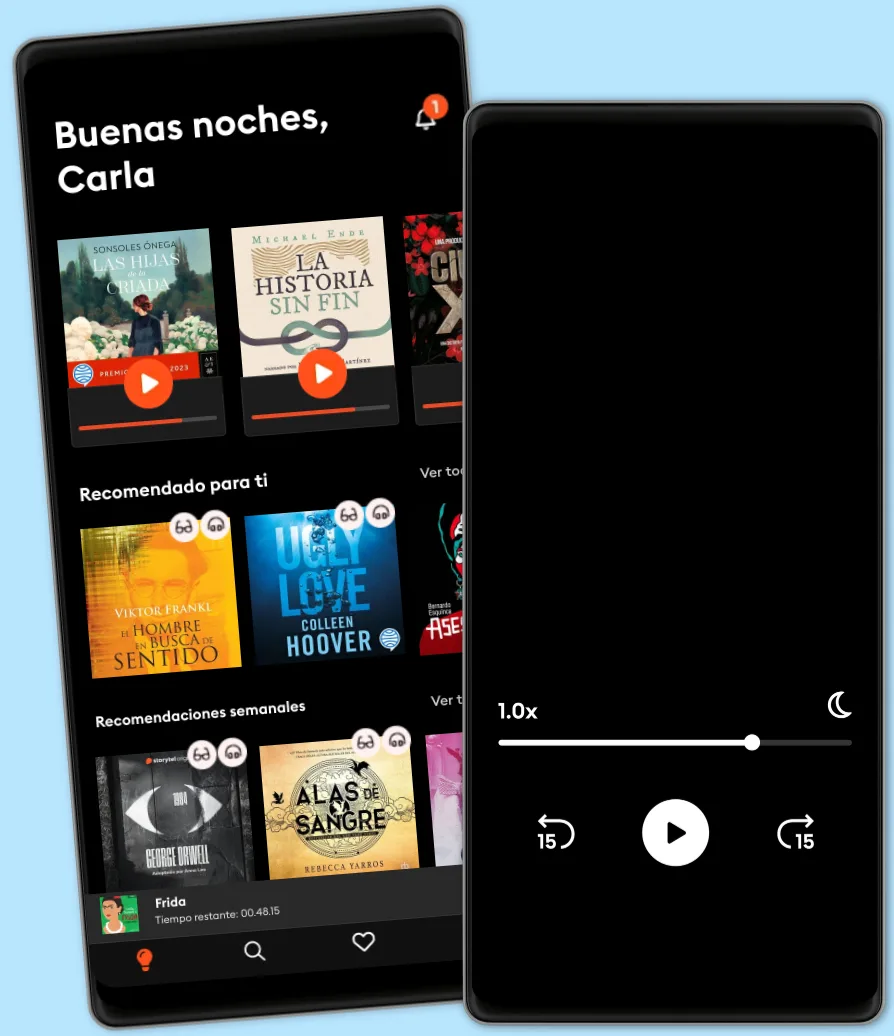
Escucha y lee
Descubre un mundo infinito de historias
- Lee y escucha todo lo que quieras
- Más de 1 millón de títulos
- Títulos exclusivos + Storytel Originals
- Precio regular: CLP 7,990 al mes
- Cancela cuando quieras
Otros podcasts que te pueden gustar...
- Intelligence SquaredIntelligence Squared
- A vivir que son dos díasSER Podcast
- SerendipiasSER Podcast
- La Hora ExtraSER Podcast
- Hoy por HoySER Podcast
- Un Libro Una HoraSER Podcast
- Still Online - La nostra eredità digitaleBeatrice Petrella
- The DailyThe New York Times
- This American LifeThis American Life
- The Witch Trials of J.K. RowlingThe Free Press
- Intelligence SquaredIntelligence Squared
- A vivir que son dos díasSER Podcast
- SerendipiasSER Podcast
- La Hora ExtraSER Podcast
- Hoy por HoySER Podcast
- Un Libro Una HoraSER Podcast
- Still Online - La nostra eredità digitaleBeatrice Petrella
- The DailyThe New York Times
- This American LifeThis American Life
- The Witch Trials of J.K. RowlingThe Free Press
Español
Chile