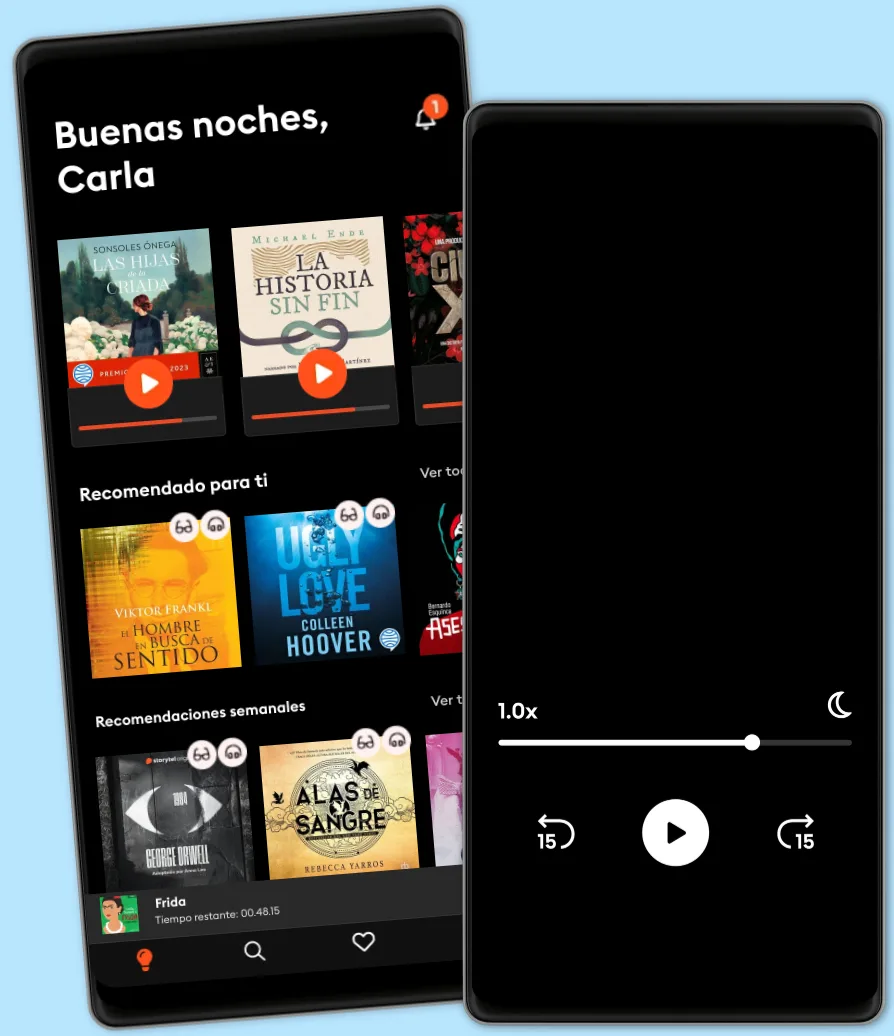
Escucha y lee
Descubre un mundo infinito de historias
- Lee y escucha todo lo que quieras
- Más de 1 millón de títulos
- Títulos exclusivos + Storytel Originals
- 7 días de prueba gratis, luego $169 MXN al mes
- Cancela cuando quieras
ETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking world
- Por
- Editor
- Idioma
- Inglés
- Formato
- Categoría
No ficción
Ethical hacking, also known as penetration testing or white-hat hacking, is a practice of deliberately probing and assessing the security of computer systems, networks, applications, and other digital environments in order to identify vulnerabilities and weaknesses that could potentially be exploited by malicious hackers. The primary goal of ethical hacking is to proactively uncover these vulnerabilities before they can be exploited by unauthorized individuals or groups, thereby helping organizations strengthen their security measures and protect their sensitive information. Key aspects of ethical hacking include: Authorization: Ethical hackers must obtain proper authorization from the owner or administrator of the system before conducting any tests. This ensures that the testing process remains within legal and ethical boundaries. Methodology: Ethical hacking involves a systematic and structured approach to identify vulnerabilities. This includes various techniques like network scanning, penetration testing, social engineering, and vulnerability assessment. Scope: The scope of an ethical hacking engagement is defined before the testing begins. It outlines the systems, applications, and networks that will be tested. Staying within the defined scope ensures that only authorized systems are tested. Information Gathering: Ethical hackers gather information about the target systems, including their architecture, software versions, and potential weak points. This information helps them plan their testing approach. Vulnerability Analysis: Ethical hackers use various tools and techniques to identify vulnerabilities, misconfigurations, and weak points in the target systems. These vulnerabilities could include software bugs, insecure configurations, or design flaws. Exploitation: In a controlled environment, ethical hackers might attempt to exploit the identified vulnerabilities to demonstrate the potential impact of a real attack. However, they stop short of causing
© 2023 BookRix (Ebook): 9783755451433
Fecha de lanzamiento
Ebook: 29 de agosto de 2023
Etiquetas
- Harry Potter y la piedra filosofal J.K. Rowling
4.8
- Por si un día volvemos María Dueñas
4.6
- Harry Potter y la cámara secreta J.K. Rowling
4.8
- Harry Potter y el prisionero de Azkaban J.K. Rowling
4.9
- Los secretos de la mente millonaria T. Harv Eker
4.3
- Perras de reserva Dahlia de la Cerda
4.5
- Harry Potter y la Orden del Fénix J.K. Rowling
4.8
- El Cuervo: Sonido 3D Edgar Alan Poe
4.3
- Harry Potter y el cáliz de fuego J.K. Rowling
4.9
- Emma bajo el cielo de Omán Jean Reno
3.5
- Lo Que Piensas, Lo Creas: El poder invisible de tus palabras, tu mente y tu energía para transformar tu realidad desde adentro Tus Decretos
4.7
- Harry Potter y el misterio del príncipe J.K. Rowling
4.9
- Harry Potter y las Reliquias de la Muerte J.K. Rowling
4.9
- Fabricación Ricardo Raphael
4.6
- Como ser un imán para las personas Marc Reklau
4.4
Explora nuevos mundos
Más de 1 millón de títulos
Modo sin conexión
Kids Mode
Cancela en cualquier momento
Ilimitado
Escucha y lee sin límites.
$169 /mes
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
Ilimitado Anual
Escucha y lee sin límites a un mejor precio.
$1190 /año
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
Familiar
Perfecto para compartir historias con toda la familia.
Desde $259 /mes
Acceso a todo el catálogo
Modo sin conexión + Kids Mode
Cancela en cualquier momento
$259 /mes
Español
México