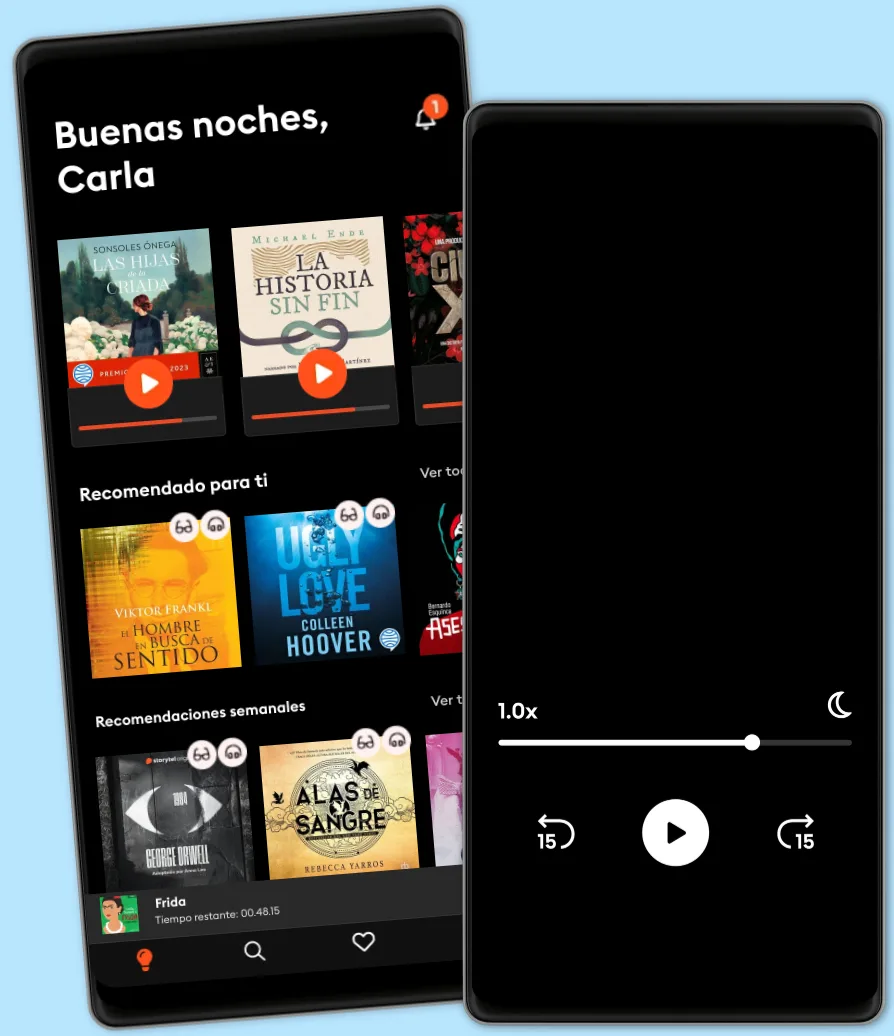
Escucha y lee
Descubre un mundo infinito de historias
- Lee y escucha todo lo que quieras
- Más de 1 millón de títulos
- Títulos exclusivos + Storytel Originals
- 7 días de prueba gratis, luego $7.99 /mes
- Cancela cuando quieras
Kali Linux Intrusion and Exploitation Cookbook: Powerful recipes to detect vulnerabilities and perform security assessments
- Por
- Editor
- Idioma
- Inglés
- Formato
- Categoría
No ficción
With the increasing threats of breaches and attacks on critical infrastructure, system administrators and architects can use Kali Linux 2.0 to ensure their infrastructure is secure by finding out known vulnerabilities and safeguarding their infrastructure against unknown vulnerabilities.
This practical cookbook-style guide contains chapters carefully structured in three phases – information gathering, vulnerability assessment, and penetration testing for the web, and wired and wireless networks. It's an ideal reference guide if you’re looking for a solution to a specific problem or learning how to use a tool. We provide hands-on examples of powerful tools/scripts designed for exploitation.
In the final section, we cover various tools you can use during testing, and we help you create in-depth reports to impress management. We provide system engineers with steps to reproduce issues and fix them.
© 2017 Packt Publishing (Ebook): 9781783982172
Fecha de lanzamiento
Ebook: 21 de abril de 2017
Etiquetas
Otros también disfrutaron...
- Por si un día volvemos María Dueñas
4.6
- El Gran Arcano Paloma Sánchez-Garnica
4
- Mi recuerdo es más fuerte que tu olvido: Premio de Novela Fernando Lara 2016 Paloma Sánchez-Garnica
4.4
- La última huella Marcos Nieto Pallarés
4.2
- El alma de las piedras Paloma Sánchez-Garnica
4.3
- Solas en el silencio Silvia Intxaurrondo
4.2
- Un golpecito en la ventanilla Linwood Barclay
4.1
- La saga de los longevos 3. El Camino del Padre Eva García Sáenz de Urturi
4.2
- Pecados 4. Rey de la desidia Ana Huang
4
- Pecados 3. Rey de la codicia Ana Huang
3.9
- La protegida Rafael Tarradas Bultó
4.5
- Corazón de oro Luz Gabás
4.3
- La reina sin espejo Lorenzo Silva
4.3
- Brujería para chicas descarriadas Grady Hendrix
4.3
- Mi querida Lucía La Vecina Rubia
4
Explora nuevos mundos
Más de 1 millón de títulos
Modo sin conexión
Kids Mode
Cancela en cualquier momento
Unlimited
Para los que quieren escuchar y leer sin límites.
1 cuenta
Acceso ilimitado
Escucha y lee los títulos que quieras
Modo sin conexión + Modo Infantil
Cancela en cualquier momento
Español
América Latina