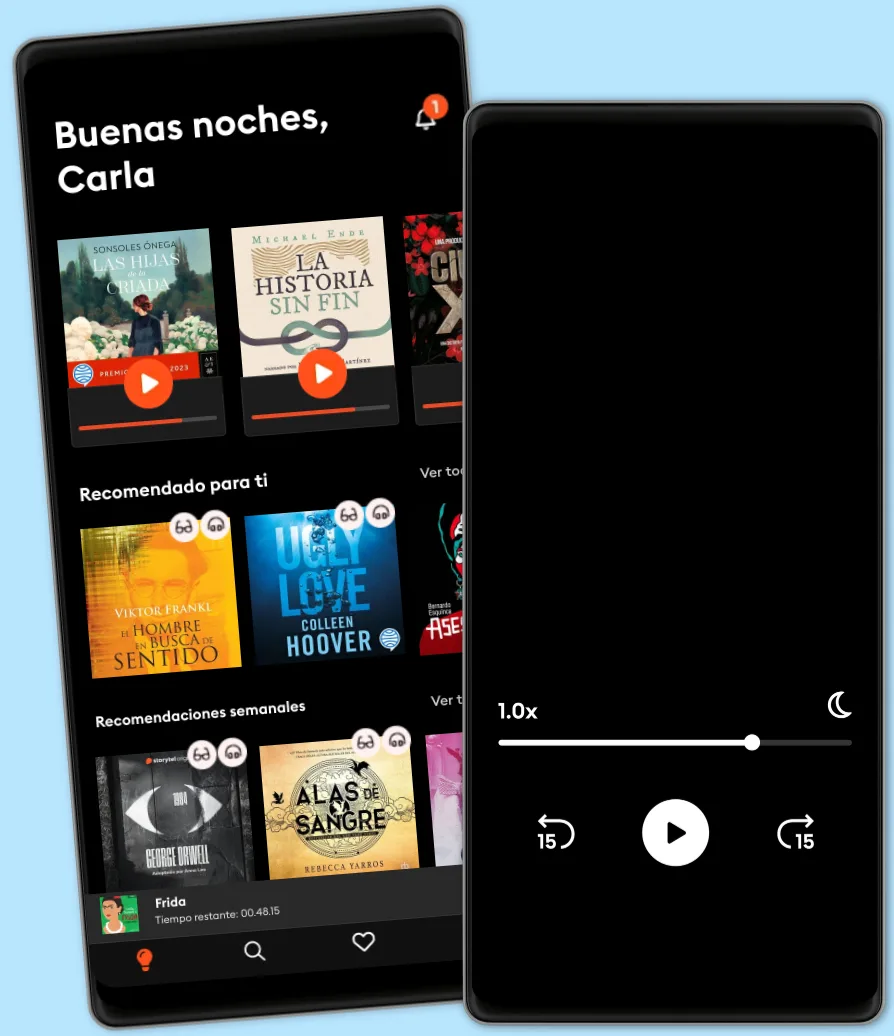
Escucha y lee
Descubre un mundo infinito de historias
- Lee y escucha todo lo que quieras
- Más de 1 millón de títulos
- Títulos exclusivos + Storytel Originals
- 7 días de prueba gratis, luego $7.99 /mes
- Cancela cuando quieras
Study Guide - 300-215 CBRFIR: Conducting Forensic Analysis and Incident Response Using Cisco Technologies for CyberSecurity Exam
- Por
- Editor
- Idioma
- Inglés
- Formato
- Categoría
No ficción
The 300-215 CBRFIR exam focuses on conducting forensic analysis and incident response using Cisco technologies to effectively detect, investigate, and respond to cybersecurity incidents. This certification covers a comprehensive range of topics, beginning with foundational concepts of digital forensics and incident response, including the principles and phases of incident handling such as preparation, identification, containment, eradication, recovery, and lessons learned. Legal considerations and maintaining the chain of custody for digital evidence are emphasized to ensure integrity and compliance.
The guide delves into forensic techniques and procedures encompassing data collection, memory and disk forensics, network forensics, and log and artifact analysis, supported by hashing and imaging techniques for preserving evidence. Endpoint-based analysis teaches how to identify host-based indicators, analyze registries, file systems, running processes, and use Cisco Secure Endpoint (AMP) for malware detection and behavioral analysis.
Network-based analysis focuses on packet capture, protocol analysis, anomaly detection, and leveraging Cisco Secure Network Analytics (Stealthwatch) and NetFlow telemetry for threat detection. The importance of analyzing alert data and logs through normalization, correlation, and utilizing tools like Cisco SecureX and SIEMs is highlighted.
Threat hunting and intelligence integration explain methodologies for IOC enrichment, using threat intelligence platforms, open-source intelligence, and Cisco’s Threat Grid and Talos. The use of Cisco tools such as AMP, Threat Grid, Stealthwatch, and SecureX for forensics and incident response is covered thoroughly.
Finally, the guide outlines incident response playbooks, automation, best practices, compliance standards, and post-incident activities to ensure efficient and effective cybersecurity operations, supported by real-world scenarios and practice questions to reinforce learning.
© 2025 PublishDrive (Ebook): 6610000956654
Fecha de lanzamiento
Ebook: 22 de mayo de 2025
Etiquetas
Otros también disfrutaron...
- La última huella Marcos Nieto Pallarés
4.2
- La protegida Rafael Tarradas Bultó
4.5
- Corazón de oro Luz Gabás
4.3
- Las hijas de la criada: Premio Planeta 2023 Sonsoles Ónega
4.4
- No le dejes entrar Lisa Jewell
4
- Venganza Carme Chaparro
4.2
- Hamnet Maggie O'Farrell
4.5
- Mil cosas Juan Tallón
4.1
- Vera, una historia de amor: Premio Planeta 2025 Juan del Val
2.6
- Reembrujada Lucy Jane Wood
4.1
- Delito Carme Chaparro
4
- Como bestias Violaine Bérot
4.5
- Ena Pilar Eyre
3.9
- Ande, ande, ande, la Mari Morena Megan Maxwell
4.5
- Confía en lo que ves Linwood Barclay
4.4
Explora nuevos mundos
Más de 1 millón de títulos
Modo sin conexión
Kids Mode
Cancela en cualquier momento
Unlimited
Para los que quieren escuchar y leer sin límites.
$7.99 /mes
Escucha y lee los títulos que quieras
Modo sin conexión + Modo Infantil
Cancela en cualquier momento
Español
América Latina