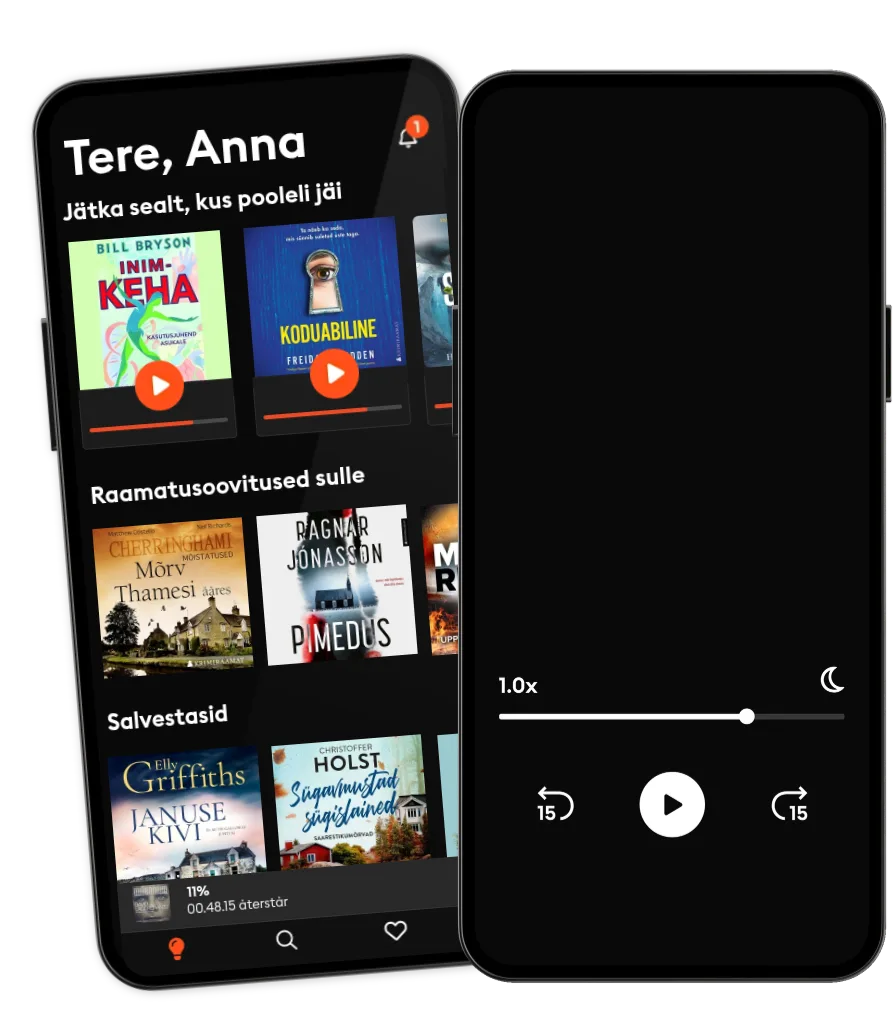
Loe ja kuula
Astu lugude lõputusse maailma
- Proovi tasuta
- Loe ja kuula nii palju, kui soovid
- Suurim valik eestikeelseid raamatuid
- Kokku üle 700 000 raamatu 4 keeles
Study Guide - 300-215 CBRFIR: Conducting Forensic Analysis and Incident Response Using Cisco Technologies for CyberSecurity Exam
- Autor
- Kirjastaja
- Keel
- inglise
- Vorming
- Kategooria
Teadmiskirjandus
The 300-215 CBRFIR exam focuses on conducting forensic analysis and incident response using Cisco technologies to effectively detect, investigate, and respond to cybersecurity incidents. This certification covers a comprehensive range of topics, beginning with foundational concepts of digital forensics and incident response, including the principles and phases of incident handling such as preparation, identification, containment, eradication, recovery, and lessons learned. Legal considerations and maintaining the chain of custody for digital evidence are emphasized to ensure integrity and compliance.
The guide delves into forensic techniques and procedures encompassing data collection, memory and disk forensics, network forensics, and log and artifact analysis, supported by hashing and imaging techniques for preserving evidence. Endpoint-based analysis teaches how to identify host-based indicators, analyze registries, file systems, running processes, and use Cisco Secure Endpoint (AMP) for malware detection and behavioral analysis.
Network-based analysis focuses on packet capture, protocol analysis, anomaly detection, and leveraging Cisco Secure Network Analytics (Stealthwatch) and NetFlow telemetry for threat detection. The importance of analyzing alert data and logs through normalization, correlation, and utilizing tools like Cisco SecureX and SIEMs is highlighted.
Threat hunting and intelligence integration explain methodologies for IOC enrichment, using threat intelligence platforms, open-source intelligence, and Cisco’s Threat Grid and Talos. The use of Cisco tools such as AMP, Threat Grid, Stealthwatch, and SecureX for forensics and incident response is covered thoroughly.
Finally, the guide outlines incident response playbooks, automation, best practices, compliance standards, and post-incident activities to ensure efficient and effective cybersecurity operations, supported by real-world scenarios and practice questions to reinforce learning.
© 2025 PublishDrive (E-raamat): 6610000956654
Väljaandmise kuupäev
E-raamat: 22. mai 2025
Sildid
- Kuidas tappa oma perekonda Bella Mackie
5
- Lilledele värsket vett Valérie Perrin
4.9
- Magamise kunst Henri Tuomilehto
5
- Hinnaline saak Christoffer Holst
4.3
- Anna O Matthew Blake
5
- Lapsehoidja Sofie Sarenbrant
4.5
- Ekraaniaju Anders Hansen
5
- Prantsuse kokanduskool Caroline James
4.3
- Kolgas Max Seeck
4.9
- Cinnamon Fallsi saladus R.L. Killmore
4.8
- Loomade farm George Orwell
- Tegevjuhi päevik Steven Bartlett
5
- Kaabaka surm M. C. Beaton
- Must rada Antonio Manzini
- Toateenija saladus Nita Prose
4.8
- Kallim Freida McFadden
4.7
- Rääkida surnutega Anna Jansson
4.6
- Lilledele värsket vett Valérie Perrin
4.9
- Anna O Matthew Blake
5
- Viimne vanne M. W. Craven
4.8
- Koduabiline jälgib sind Freida McFadden
4.9
- Joulud Westini pagaritöökojas Solja Krapu-Kallio
4
- Koduabiline Freida McFadden
4.9
- Kolgas Max Seeck
4.9
- Suvi Applemore’is Rachael Lucas
4.5
- Õpetaja Freida McFadden
4.8
- Lapsehoidja Sofie Sarenbrant
4.5
- Toateenija saladus Nita Prose
4.8
- Koduabilise saladus Freida McFadden
4.6
- Punane elavhõbe Andres Anvelt
4.7
- Kallim Freida McFadden
4.7
- Viimne vanne M. W. Craven
4.8
- Koduabiline jälgib sind Freida McFadden
4.9
- Koduabiline Freida McFadden
4.9
- Kolgas Max Seeck
4.9
- Suvi Applemore’is Rachael Lucas
4.5
- Anna O Matthew Blake
5
- Lapsehoidja Sofie Sarenbrant
4.5
- Toateenija saladus Nita Prose
4.8
- Koduabilise saladus Freida McFadden
4.6
- Pulmarahvas Alison Espach
4.6
- Kuraator M. W. Craven
5
- Avatud uksed Sofie Sarenbrant
5
- Prantsuse kokanduskool Caroline James
4.3
- Kuidas tappa oma perekonda Bella Mackie
5
Vali pakett
Kokku üle 700 000 raamatu 4 keeles
Suur valik eestikeelseid raamatuid
Uusi raamatuid iga nädal
Kids Mode lastesõbralik keskkond
Unlimited
14.99 € /kuus
Tühista igal ajal
Unlimited (aastane)
119.99 € /aasta
Säästa 33%
Eesti
Eesti