Cybersecurity - Attack and Defense Strategies: Infrastructure security with Red Team and Blue Team tactics
- Språk
- Engelsk
- Format
- Kategori
Fakta og dokumentar
The book will start talking about the security posture before moving to Red Team tactics, where you will learn the basic syntax for the Windows and Linux tools that are commonly used to perform the necessary operations. You will also gain hands-on experience of using new Red Team techniques with powerful tools such as python and PowerShell, which will enable you to discover vulnerabilities in your system and how to exploit them. Moving on, you will learn how a system is usually compromised by adversaries, and how they hack user's identity, and the various tools used by the Red Team to find vulnerabilities in a system.
In the next section, you will learn about the defense strategies followed by the Blue Team to enhance the overall security of a system. You will also learn about an in-depth strategy to ensure that there are security controls in each network layer, and how you can carry out the recovery process of a compromised system. Finally, you will learn how to create a vulnerability management strategy and the different techniques for manual log analysis.
© 2018 Packt Publishing (E-bok): 9781788473859
Utgivelsesdato
E-bok: 30. januar 2018
Tagger
- Jordmoren i Auschwitz Anna Stuart
4.8
- Jakten på en serieovergriper Anne-Britt Harsem
4.8
- Skriket Jan-Erik Fjell
4.2
- Hushjelpen Freida McFadden
4.4
- Alle mine barn, kom hjem May Lis Ruus
3.9
- Fare, fare, krigsmann May Lis Ruus
4.3
- Ta den ring og la den vandre May Lis Ruus
4.2
- Aldri være trygg May Lis Ruus
4.3
- Mirakelkuren Harlan Coben
4
- Slinger i brudevalsen Carole Matthews
3.6
- Sydney i fare Clive Cussler
4.4
- Jævla menn Andrev Walden
4.3
- Markens grøde Knut Hamsun
4.8
- Sannhetens øyeblikk Kristin Hannah
4.5
- Hushjelpens hemmelighet Freida McFadden
4.3
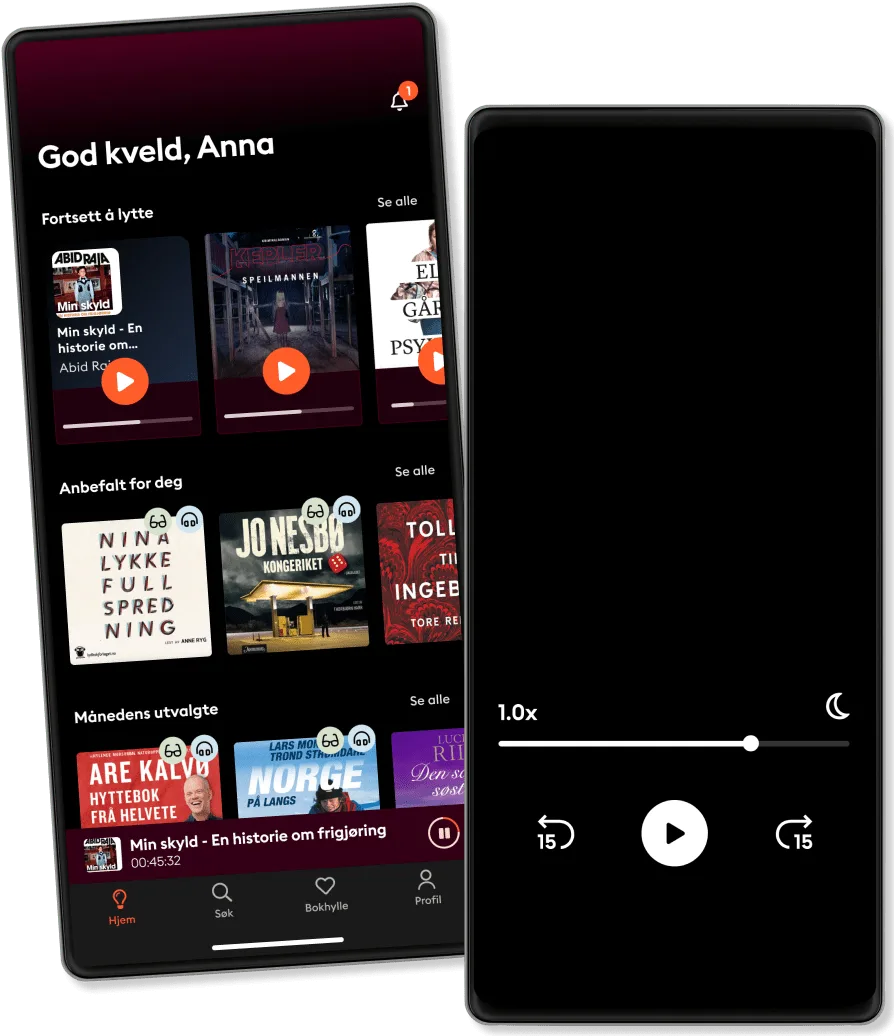
Derfor vil du elske Storytel:
Over 900 000 lydbøker og e-bøker
Eksklusive nyheter hver uke
Lytt og les offline
Kids Mode (barnevennlig visning)
Avslutt når du vil
Unlimited
For deg som vil lytte og lese ubegrenset.
1 konto
Ubegrenset lytting
Lytt så mye du vil
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Family
For deg som ønsker å dele historier med familien.
2-3 kontoer
Ubegrenset lytting
Lytt så mye du vil
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
2 kontoer
289 kr /månedPremium
For deg som lytter og leser ofte.
1 konto
50 timer/måned
Lytt opptil 50 timer per måned
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Basic
For deg som lytter og leser av og til.
1 konto
20 timer/måned
Lytt opp til 20 timer per måned
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Lytt og les ubegrenset
Kos deg med ubegrenset tilgang til mer enn 700 000 titler.
- Lytt og les så mye du vil
- Utforsk et stort bibliotek med fortellinger
- Over 1500 serier på norsk
- Ingen bindingstid, avslutt når du vil
Norsk
Norge