Hands-On Penetration Testing on Windows: Unleash Kali Linux, PowerShell, and Windows debugging tools for security testing and analysis
- Av
- Forlag
- Språk
- Engelsk
- Format
- Kategori
Fakta og dokumentar
Master the art of identifying vulnerabilities within the Windows OS and develop the desired solutions for it using Kali Linux.
Key Features
• Identify the vulnerabilities in your system using Kali Linux 2018.02
•
• Discover the art of exploiting Windows kernel drivers
•
• Get to know several bypassing techniques to gain control of your Windows environment
•
Book Description
Windows has always been the go-to platform for users around the globe to perform administration and ad hoc tasks, in settings that range from small offices to global enterprises, and this massive footprint makes securing Windows a unique challenge. This book will enable you to distinguish yourself to your clients.
In this book, you'll learn advanced techniques to attack Windows environments from the indispensable toolkit that is Kali Linux. We'll work through core network hacking concepts and advanced Windows exploitation techniques, such as stack and heap overflows, precision heap spraying, and kernel exploitation, using coding principles that allow you to leverage powerful Python scripts and shellcode.
We'll wrap up with post-exploitation strategies that enable you to go deeper and keep your access. Finally, we'll introduce kernel hacking fundamentals and fuzzing testing, so you can discover vulnerabilities and write custom exploits.
By the end of this book, you'll be well-versed in identifying vulnerabilities within the Windows OS and developing the desired solutions for them.
What you will learn
• Get to know advanced pen testing techniques with Kali Linux
•
• Gain an understanding of Kali Linux tools and methods from behind the scenes
•
• See how to use Kali Linux at an advanced level
•
• Understand the exploitation of Windows kernel drivers
•
• Understand advanced Windows concepts and protections, and how to bypass them using Kali Linux
•
• Discover Windows exploitation techniques, such as stack and heap overflows and kernel exploitation, through coding principles
•
Who this book is for
This book is for penetration testers, ethical hackers, and individuals breaking into the pentesting role after demonstrating an advanced skill in boot camps. Prior experience with Windows exploitation, Kali Linux, and some Windows debugging tools is necessary
© 2018 Packt Publishing (E-bok): 9781788295093
Utgivelsesdato
E-bok: 30. juli 2018
Tagger
Andre liker også ...
- Infrastructure Attack Strategies for Ethical Hacking Himanshu Sharma
- Summary, Analysis, and Review of Peter Schweizer's Profiles in Corruption: Abuse of Power by America's Progressive Elite Start Publishing Notes
- Summary, Analysis, and Review of Martha MacCallum's Unknown Valor: A Story of Family, Courage, and Sacrifice from Pearl Harbor to Iwo Jima Start Publishing Notes
- Summary, Analysis, and Review of Emily Ley's When Less Becomes More: Making Space for Slow, Simple, and Good Start Publishing Notes
- Skriket Jan-Erik Fjell
4.2
- Jakten på en serieovergriper Anne-Britt Harsem
4.8
- Jordmoren i Auschwitz Anna Stuart
4.8
- Hushjelpen Freida McFadden
4.4
- Perfekte forbrytelser finnes ikke Steinar H. Nygaard
4.1
- Stormberget Liza Marklund
4
- Piken på toget Paula Hawkins
3.9
- Markens grøde Knut Hamsun
4.8
- Appelsinparken Merete Lien
3.9
- Hushjelpens hemmelighet Freida McFadden
4.3
- Makten og æren Henrik H. Langeland
4.3
- Hemmeligheten Lee Child
3.8
- Tørt land Jørn Lier Horst
4.3
- Ektepakten Simona Ahrnstedt
3.9
- Polarsirkelen Liza Marklund
3.8
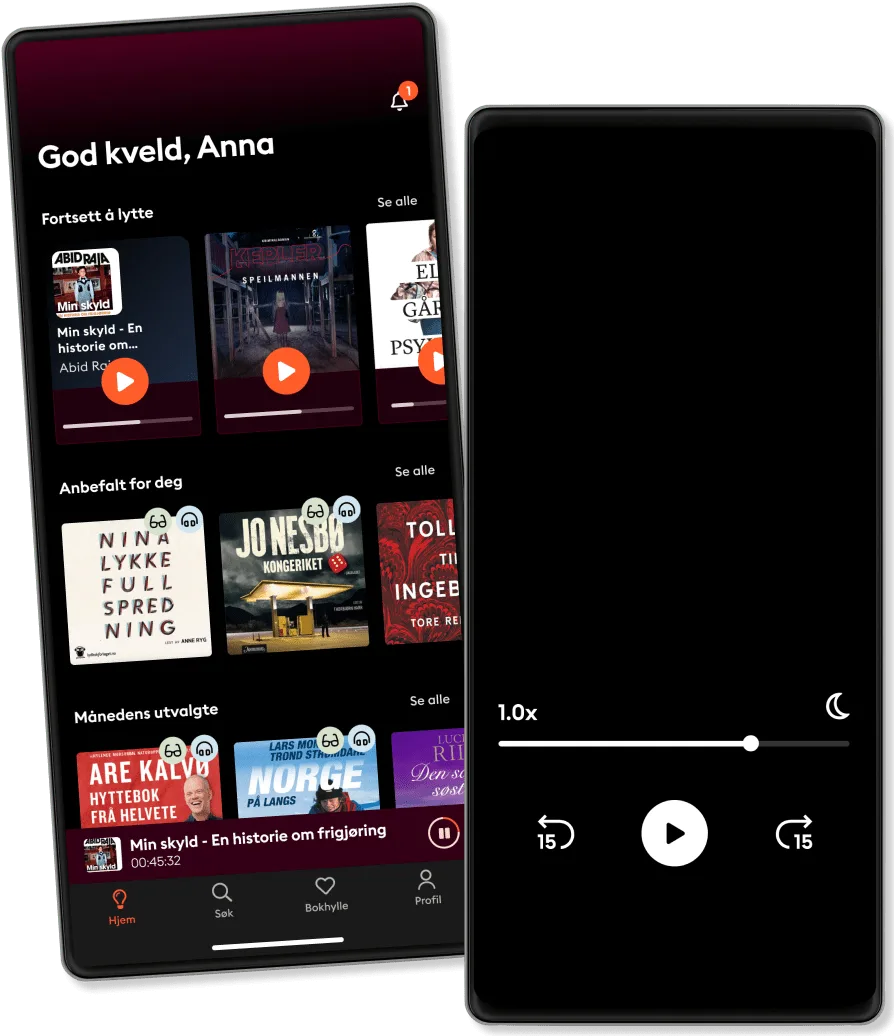
Derfor vil du elske Storytel:
Over 900 000 lydbøker og e-bøker
Eksklusive nyheter hver uke
Lytt og les offline
Kids Mode (barnevennlig visning)
Avslutt når du vil
Unlimited
For deg som vil lytte og lese ubegrenset.
219 kr /måned
Lytt så mye du vil
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Family
For deg som ønsker å dele historier med familien.
Fra 289 kr /måned
Lytt så mye du vil
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
289 kr /måned
Premium
For deg som lytter og leser ofte.
189 kr /måned
Lytt opptil 50 timer per måned
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Basic
For deg som lytter og leser av og til.
149 kr /måned
Lytt opp til 20 timer per måned
Over 900 000 bøker
Nye eksklusive bøker hver uke
Avslutt når du vil
Lytt og les ubegrenset
Kos deg med ubegrenset tilgang til mer enn 700 000 titler.
- Lytt og les så mye du vil
- Utforsk et stort bibliotek med fortellinger
- Over 1500 serier på norsk
- Ingen bindingstid, avslutt når du vil
Norsk
Norge