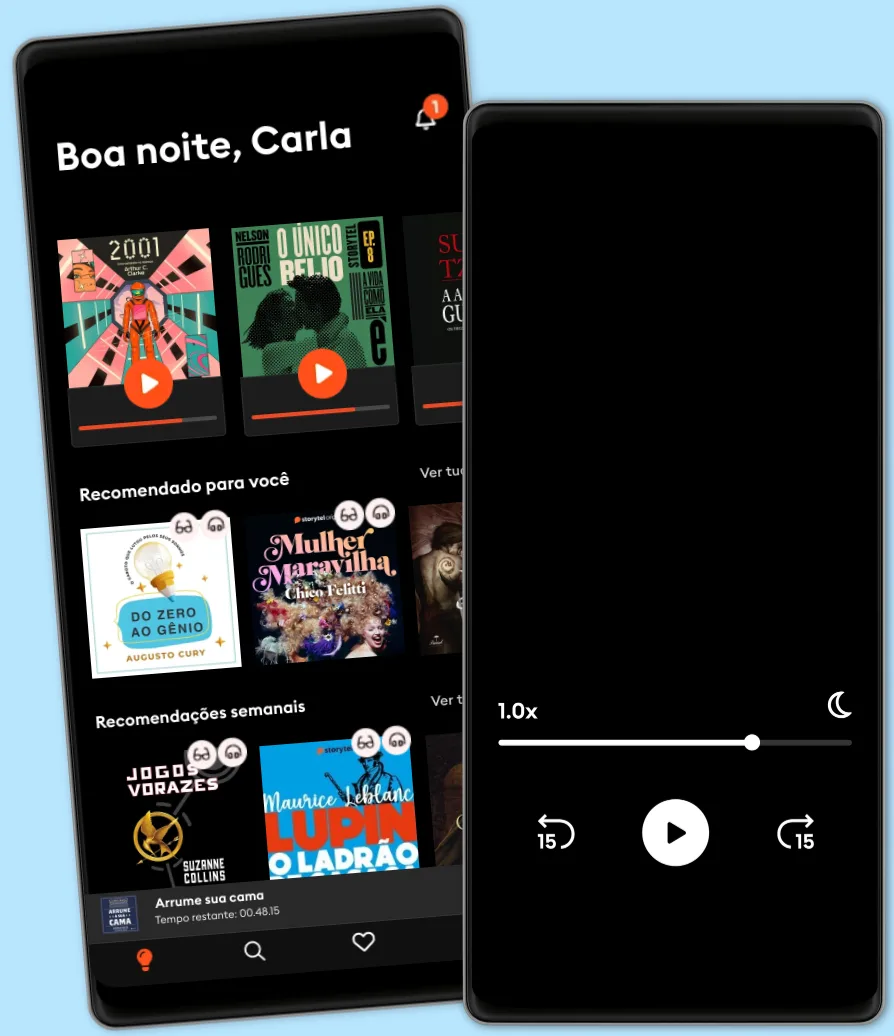
Ouça e leia
Entre em um mundo infinito de histórias
- Ler e ouvir tanto quanto você quiser
- Com mais de 500.000 títulos
- Títulos exclusivos + Storytel Originals
- 7 dias de teste gratuito, depois R$19,90/mês
- Fácil de cancelar a qualquer momento
HACKING: 3 BOOKS IN 1
- Por
- Com:
- Editor
- 4 Avaliações
4.5
- Duração
- 11H 20min
- Idioma
- Inglês
- Formato
- Categoria
Não-ficção
THIS AUDIOBOOK INCLUDES 3 MANUSCRIPTS:
- BOOK 1: Hacking with Kali Linux: Penetration Testing Hacking Bible
- BOOK 2: Social Engineering Attacks, Techniques & Prevention
- BOOK 3: Hacking Firewalls & Bypassing Honeypots
In order to understand hackers and protect the network infrastructure you must think like a hacker in today’s expansive and eclectic internet and you must understand that nothing is fully secured. This audiobook will focus on some of the most dangerous hacker tools that are favorite of both, White Hat and Black Hat hackers.
If you attempt to use any of the tools discussed in this book on a network without being authorized and you disturb or damage any systems, that would be considered illegal black hat hacking. So, I would like to encourage all readers to deploy any tool described in this book for WHITE HAT USE ONLY.
BUY THIS BOOK NOW AND GET STARTED TODAY!
IN THIS BOOK YOU WILL LEARN:
•How to Install Kali Linux & TOR
•How to use BurpSuite for various attacks
•SSL & CMS Scanning Techniques
•Port Scanning & Network Sniffing
•How to Configure SPAN
•How to implement SYN Scan Attack
•How to Brute Force with Hydra
•How to use Low Orbit ion Cannon
•How to use Netcat, Meterpreter, Armitage, SET
•How to deploy Spear Phishing & PowerShell Attack
•How to deploy various Wireless Hacking Attacks
•Phishing, Vishing, Smishing, Spear Phishing and Whaling
•Executing the Social Engineering Attack
•In-person social engineering techniques
•Dumpster Diving & Data Breaches
•Phishing Page Types
•Filter Evasion Techniques
•How to use PhishTank and Phish5
•Identity Theft and Impersonation
•Fragmentation attack
•Overlapping Fragments Attack
•Time-to-Live attack
•DoS Attack & Flooding Attack
© 2020 Alex Wagner (Audiobook): 9781839381201
Data de lançamento
Audiobook: 27 de março de 2020
Outros também usufruíram...
- Linux for Beginners: How to Perform Linux Admin Tasks ATTILA KOVACS
- Computer Programming and Cybersecurity for Beginners: All You Need to Know to Get Started with Python for Data Science, Excel and Ethical Hacking Kevin Clark
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network Security Hans Weber
- Cloud Security For Dummies Ted Coombs
- Hacking: How to Hack Alex Wagner
- (ISC)2 CCSP Certified Cloud Security Professional Official Study Guide, 3rd Edition Mike Chapple
- The Ultimate Kali Linux Book - Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and Empire Glen D. Singh
- Grokking Algorithms: A Complete Beginner’s Guide for the Effective Learning of Algorithms Dylan Christian
- Effective Machine Learning Teams: Best Practices for ML Practitioners David Colls
- Big Brain Revolution: Artificial Intelligence – Spy or Saviour? Dr Michelle Tempest
- Hacking AI: Big and Complete Guide to Hacking, Security, AI and Big Data. Hans Weber
- Computer Science 2.0 Beginners Crash Course - Python, Javascript, Cyber Security And Algorithms: AI,programming,advance technology,matrix ,data analysis Ian Bat
- Big Data: A Complete Guide to the Basic Concepts in Data Science, Cyber Security, Analytics and Metrics Hans Weber
- CompTIA A+ Certification Study Guide For 220-1102 Exam 2 Books In 1: Operating Systems, Software Troubleshooting, Security Awareness & Operational Procedures HISTORY FOREVER
- Computer Systems and Networking for Beginners: Advanced Strategies and Techniques in Computer Systems and Networking for Optimal Efficiency and Scalability Saimon Carrie
- Deep Learning: Guide for Machine Learning, Neural Networks, and Data Analytics David Feldspar
- Docker Unveiled: The Comprehensive Handbook to Streamlined Development William Drake
- Artificial Intelligence: What You Need to Know About Machine Learning, Robotics, Deep Learning, Recommender Systems, Internet of Things, Neural Networks, Reinforcement Learning, and Our Future Neil Wilkins
- Big Data: Mining and Measuring Big Data for Information and Intelligence David Feldspar
- Artificial Intelligence: How Machine Learning, Robotics, and Automation Have Shaped Our Society John Adamssen
- Machine Learning For Beginners: A Comprehensive, Step-by-Step Guide to Learning and Understanding Machine Learning Concepts, Technology and Principles for Beginners Peter Bradley
- Greatest Hackers in the History Introbooks Team
- Big Data and Artificial Intelligence: Complete Guide to Data Science, AI, Big Data and Machine Learning. Hans Weber
- Artificial Intelligence: What Human Machines Will Do in the Future Quinn Spencer
- Quick Start Kubernetes Nigel Poulton
- Ultimate Kali Linux Book, Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and Empire Gllen D. Singh
- Computer Systems and Networking for Beginners: A Comprehensive Beginner's Guide to understanding Computer Systems, Networking Essentials, and the Foundations of Digital Connectivity Saimon Carrie
- Machine Learning: Understanding Big Data, Text Analytics, and Deep Learning David Feldspar
- Algorithms: 3 books in 1 : Practical Guide To Learn Algorithms for Beginners + Design Algorithms to Solve Common Problems + Advanced Data Structures for Algorithms Andy Vickler
- The Ai Revolution: Machines, Minds, and the Human Future Mustafa Scales
- Quantum Mechanics and Quantum Information Theory: Understanding the Fundamentals and Potential Applications of Quantum Mechanics and Quantum Information Theory Daniel Garfield
- Computer Science: The Complete Guide to Principles and Informatics Jonathan Rigdon
- Fundamentals of Machine Learning: A no code no math book on understanding fundamentals of modern ML & AI DSA Shots
- Software Designing and Development. Clear Guide for Beginners: Unlocking the Secrets of Software Design and Development for Beginners James Ferry
- CompTIA A+ Certification Study Guide for 220-1102 Exam: Beginners guide to Operating Systems & Software Troubleshooting Richie Miller
- Artificial Intelligence: The Complete Beginner’s Guide to the Future of A.I. John Adamssen
- History of Internet Introbooks Team
- Hacking: A Quick and Simple Introduction to the Basics of Hacking, Scripting, Cybersecurity, Networking, and System Penetration Hans Weber
- The Future Internet: How the Metaverse, Web 3.0, and Blockchain Will Transform Business and Society Bernard Marr
- Agile Project Management with Scrum: How to Become a Great Project Manager Alex Campbell
- Robotics and Artificial Intelligence Prasun Barua
- Linux for Beginners: 3 BOOKS IN 1 ATTILA KOVACS
- AI Explained: Facts, Fiction and Future Nigel Poulton
- Ethical Hacking Introbooks Team
- Mastering Blockchain: Unlocking the Power of Cryptocurrencies, Smart Contracts, and Decentralized Applications Daniel Cawrey
- GROKKING ALGORITHMS: A Comprehensive Beginner's Guide, Tips and Tricks, Simple and Effective methods and Advanced methods to learn and use Grokking Algorithms and Data structures for Programming Eric Schmidt
- Artificial Intelligence Introbooks Team
- Extreme Programming for Beginners: Embracing Agility, Quality, and Collaboration in Software Development Daniel Green
- Reprogramming The American Dream: From Rural America to Silicon Valley—Making AI Serve Us All Greg Shaw
- Electrics: Fundamentals of Electrical and Mechanical Engineering (2 in 1) Phil Gilberts
- Machine Learning: Unlocking Patterns and Insights with Advanced Algorithms Victor Sage
- CISSP And Cybersecurity For Beginners: Penetration Testing And Ethical Hacking Techniques To Defend Your Infrastructure 3 Books In 1 John Knowles
- Quantum Computers Introbooks Team
- Artificial Intelligence in Education Introbooks Team
- Cybersecurity for Beginners: Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide Kevin Clark
- Androids: The Team that Built the Android Operating System Chet Haase
- Hacking API: Navigating the Intricacies of API Security and Ethical Hacking James Ferry
- Mastering Complexity: A Comprehensive Guide to Big O Complexity and DSA Problem Solving DSA Shots
- Artificial Intelligence and Future of Business ProBusinessEducation Team
- CompTIA Security+ All-in-One Exam Guide, Sixth Edition (Exam SY0-601) Wm. Arthur Conklin
- Defensive Security Handbook: Best Practices for Securing Infrastructure (2nd Edition) Amanda Berlin
- Biomedical Engineering: The Fundamentals of Biotechnology Phil Gilberts
- Cloud-Native Architectures: Building Scalable, Resilient, and Agile Systems. Book 2 James Ferry
- Edge Computing: Revolutionizing Data Processing at the Network Edge James Ferry
- Pratique o poder do "Eu posso" Bruno Gimenes
4.5
- 18 Maneiras De Ser Uma Pessoa Mais Interessante Tom Hope
4
- O sonho de um homem ridículo Fiódor Dostoiévski
4.7
- Gerencie suas emoções Augusto Cury
4.5
- 10 Maneiras de manter o foco James Fries
3.8
- Harry Potter e a Pedra Filosofal J.K. Rowling
4.9
- Os "nãos" que você não disse Patrícia Cândido
4.2
- A gente mira no amor e acerta na solidão Ana Suy
4.5
- A metamorfose Franz Kafka
4.4
- Mais esperto que o diabo: O mistério revelado da liberdade e do sucesso Napoleon Hill
4.7
- A arte da guerra Sun Tzu
4.6
- Jogos vorazes Suzanne Collins
4.8
- Primeiro eu tive que morrer Lorena Portela
4.3
- Pare de Procrastinar: Supere a preguiça e conquiste seus objetivos Giovanni Rigters
4.3
- talvez a sua jornada agora seja só sobre você: crônicas Iandê Albuquerque
4.5
Português
Brasil