PAM Mastery
- Oleh
- Penerbit
Pluggable Authentication Modules: Threat or Menace?
PAM is one of the most misunderstood parts of systems administration. Many sysadmins live with authentication problems rather than risk making them worse. PAM’s very nature makes it unlike any other Unix access control system.
If you have PAM misery or PAM mysteries, you need PAM Mastery!
With PAM Mastery, you’ll understand:
• the different versions of PAM • the intricacies of Linux-PAM and OpenPAM • how PAM policies make decisions • how to debug PAM • the most frequently seen PAM modules • Linux-PAM extended controls and substacks • time-based one-time passwords • using SSH keys for more than SSH • password quality testing • policies from CentOS, Debian, and FreeBSD • and more!
Transform PAM from a headache to an ally with PAM Mastery
© 2018 Tilted Windmill Press (buku elektronik ): 6610000105212
Tanggal rilis
buku elektronik : 15 September 2018
PAM Mastery
- Oleh
- Penerbit
Pluggable Authentication Modules: Threat or Menace?
PAM is one of the most misunderstood parts of systems administration. Many sysadmins live with authentication problems rather than risk making them worse. PAM’s very nature makes it unlike any other Unix access control system.
If you have PAM misery or PAM mysteries, you need PAM Mastery!
With PAM Mastery, you’ll understand:
• the different versions of PAM • the intricacies of Linux-PAM and OpenPAM • how PAM policies make decisions • how to debug PAM • the most frequently seen PAM modules • Linux-PAM extended controls and substacks • time-based one-time passwords • using SSH keys for more than SSH • password quality testing • policies from CentOS, Debian, and FreeBSD • and more!
Transform PAM from a headache to an ally with PAM Mastery
© 2018 Tilted Windmill Press (buku elektronik ): 6610000105212
Tanggal rilis
buku elektronik : 15 September 2018
Yang lain juga menikmati...
- Ultimate Kali Linux Book, Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and EmpireGllen D. Singh
- Learn Docker – Fundamentals of Docker 19.x: Build, test, ship, and run containers with Docker and Kubernetes, 2nd EditionGabriel N. Schenker
- Docker Decoded: Docker Programming Demystified: Step-by-Step Methods for BeginnersSarah Carter
- Wee Willie WinkieRudyard Kipling
- South Sea TalesJack London
- Man in the Blue MoonMichael Morris
- Mastering Vim: Build a software development environment with Vim and NeovimRuslan Osipov
- Richest Man In Babylon - Original EditionGeorge S Clason
- Summary of John Stryker Meyer's Across The FenceDistill Books
- Summary of Robin K. Dreeke's It's Not All About "Me"Distill Books
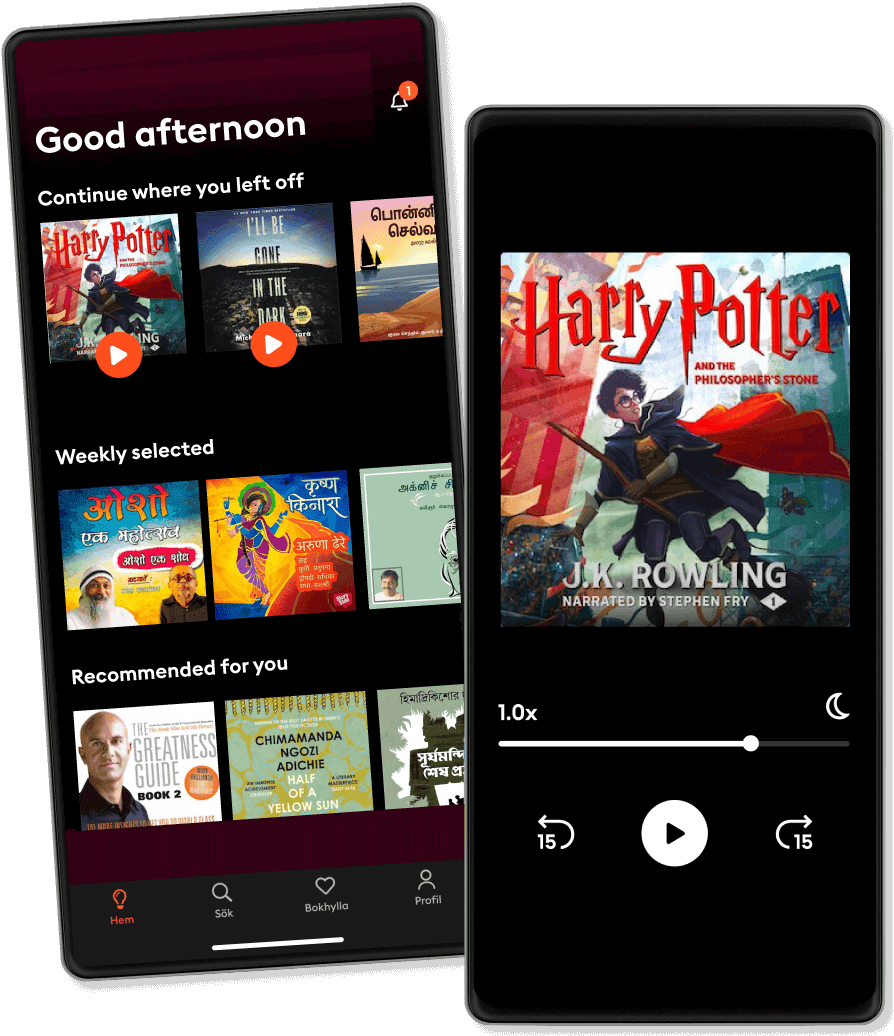
Dengarkan dan baca
Masuki dunia cerita tanpa batas
- Baca dan dengarkan sebanyak yang Anda mau
- Lebih dari 1 juta judul
- Judul eksklusif + Storytel Original
- Uji coba gratis 14 hari, lalu €9,99/bulan
- Mudah untuk membatalkan kapan saja
Rating dan ulasan
Sekilas ulasan
Belum ada ulasan
Unduh aplikasinya untuk bergabung dalam percakapan dan menambahkan ulasan.
Bahasa Indonesia
Indonesia