We Need To Talk: 52 Weeks To Better Cyber-Security
- بواسطة
- الناشر
- اللغة
- اللغة الإنجليزية
- Format
- الفئة
كتب واقعية
The book provides a comprehensive approach to discussing cyber-security, addressing topics such as risk management, configuration management, vulnerability management, policy, threat intelligence, and incident response. The discussions that are sparked will lead to helping your team strengthen and mature your organization's security posture.
The book is designed for information security professionals and their teams looking for a structured way to improve their organization’s cyber-security posture over one year. It is an ideal resource for those teams who wish to develop a well-rounded understanding of cyber-security and gain insight into the various elements that are needed for a successful program.
*This book was written programmatically with the help of AI tools and edited using Grammarly.
© 2023 PublishDrive (كتاب ): 6610000436200
تاريخ الإصدار
كتاب : ١٠ رجب ١٤٤٤ هـ
الوسوم
We Need To Talk: 52 Weeks To Better Cyber-Security
- بواسطة
- الناشر
- اللغة
- اللغة الإنجليزية
- Format
- الفئة
كتب واقعية
The book provides a comprehensive approach to discussing cyber-security, addressing topics such as risk management, configuration management, vulnerability management, policy, threat intelligence, and incident response. The discussions that are sparked will lead to helping your team strengthen and mature your organization's security posture.
The book is designed for information security professionals and their teams looking for a structured way to improve their organization’s cyber-security posture over one year. It is an ideal resource for those teams who wish to develop a well-rounded understanding of cyber-security and gain insight into the various elements that are needed for a successful program.
*This book was written programmatically with the help of AI tools and edited using Grammarly.
© 2023 PublishDrive (كتاب ): 6610000436200
تاريخ الإصدار
كتاب : ١٠ رجب ١٤٤٤ هـ
الوسوم
واستمتع آخرون أيضًا...
- The Secure Board: How To Be Confident That Your Organisation Is Cyber SafeClaire Pales
- The Cyber-Elephant In The Boardroom: Cyber-Accountability With The Five Pillars Of Security FrameworkMathieu Gorge
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for BusinessKim Crawley
- Cybersecurity Fundamentals: How to Establish Effective Security Management FunctionsJohn Knowles
- Cyber Security for Decision MakersKlaus Majewski
- The Secure CiO: How to Hire and Retain Great Cyber Security Talent to Protect your OrganisationClaire Pales
- Building a Cyber Resilient Business: A cyber handbook for executives and boardsShamane Tan
- International Conflicts in Cyberspace - Battlefield of the 21st Century: Cyber Attacks at State Level, Legislation of Cyber Conflicts, Opposite Views by Different Countries on Cyber Security Control & Report on the Latest Case of Russian Hacking of Government SectorsU.S. Department of Defense
- Ultimate Penetration Testing with NmapTravis DeForge
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1John Knowles
- ملخص كتاب الذكاء العاطفيترافيس برادبيري3.3
- ملخص كتاب كيف تتحدث مع أي شخص 92 خدعة صغيرة: اثنتان وتسعون خدعة صغيرة، لنجاح كبير في العلاقاتليل لاوندز3.4
- 30 يوما مع اللهفيصل أحمد بخاري4.6
- صخب الخسيف - دراما صوتية - E01أسامة المسلم4.3
- خوفأسامة المسلم4.5
- أغنية الجليد والنار: لعبة العروشجورج ر. ر. مارتن4.6
- ملخص كتاب فن الإغواء - الجزء الأولروبرت غرين4.2
- ملخص كتاب دماغك تحت تأثير الإباحيةغاري ويلسون4.1
- خوف 2أسامة المسلم4.5
- فن اللامبالاة: لعيش حياة تخالف المألوفمارك مانسون4.3
- أرض زيكولاعمرو عبدالحميد4.2
- ملخص كتاب عقل هادئ: كيف توقف التوتر وتحدّ من نوبات القلق وتقضي على التفكير السلبيستيف سكوت4.4
- فن التعامل مع الناسديل كارنيجي4.3
- أبابيلأحمد آل حمدان4.3
- العادات الذريةجيمس كلير4.5
- فن الكلامد. إيهاب فكري4.1
- ملخص كتاب الأب الغني الأب الفقيرروبرت كيوساكى3.8
- أغنية الجليد والنار: عاصفة السيوفجورج ر. ر. مارتن4.7
- طرف مجهول - الحلقة ١مصطفى التلواني4.3
- ملخص كتاب قوانين الكاريزماكيرت مورتنسن4.3
- لأنك اللهعلي بن جابر الفيفي4.8
- أوراق شمعون المصري الموسم الأولأسامة عبد الرءوف الشاذلي4.6
- فاتتني صلاة (الإصدار الصوتي الثاني)إسلام جمال4.8
- أغنية الجليد والنار: صدام الملوكجورج ر. ر. مارتن4.7
- لكنودإسلام جمال4.7
- ملخص كتاب فن اللامبالاةمارك مانسون4
- أغنية الجليد والنار: رقصة مع التنانينجورج ر. ر. مارتن4.7
- المطاردحسن الجندي4.5
- خوف - دراماأسامة المسلم4.6
- حلم رجل مضحكفيودور دوستويفسكي3.9
- طرف مجهول - الحلقة ٢مصطفى التلواني4.4
- ملخص كتاب فن الإغواء -الجزء الثانيروبرت غرين4.3
- الطفلة إيمانحزام بن راشد4.4
- الدحيحة - غزو أمريكاطاهر المعتز بالله4.6
- الخيميائيباولو كويلو4.2
- فاتتني صلاةإسلام جمال4.7
- أوراق شمعون المصري الموسم الثانيأسامة عبد الرءوف الشاذلي4.6
- حالات نادرةعبدالوهاب السيد الرفاعي4.3
- لأنك الله: رحلة إلى السماء السابعةعلي بن جابر الفيفي4.7
- ابدأ بالأهم ولو كان صعبا (التهم هذا الضفدع) : 21 طريقة ناجحة للقضاء على التسويف وإنجاز العمل بأقصر وقتبرايان تريسي4.2
- أسطورة أحمد خالد توفيق - E01خلف جابر4.4
- عداء الطائرة الورقیةخالد حسیني4.5
- قمر زمان والأميرة بدورمريم عبد العزيز3.9
- صاحب الظل الطويلجين ويبستر4.3
- ممارسة قوة الآنإكهارت تول4
- عشقني عفريت من الجنبدر رمضان4.3
- طرف مجهول - الحلقة ٣مصطفى التلواني4.5
- أوراق شمعون المصري الموسم الثالثأسامة عبد الرءوف الشاذلي4.8
- القيصر: التاريخ السري لفلاديمير بوتينطاهر المعتز بالله4.6
- ملخص كتاب لا تهتم بصغائر الأمورريتشارد كارلسون4.6
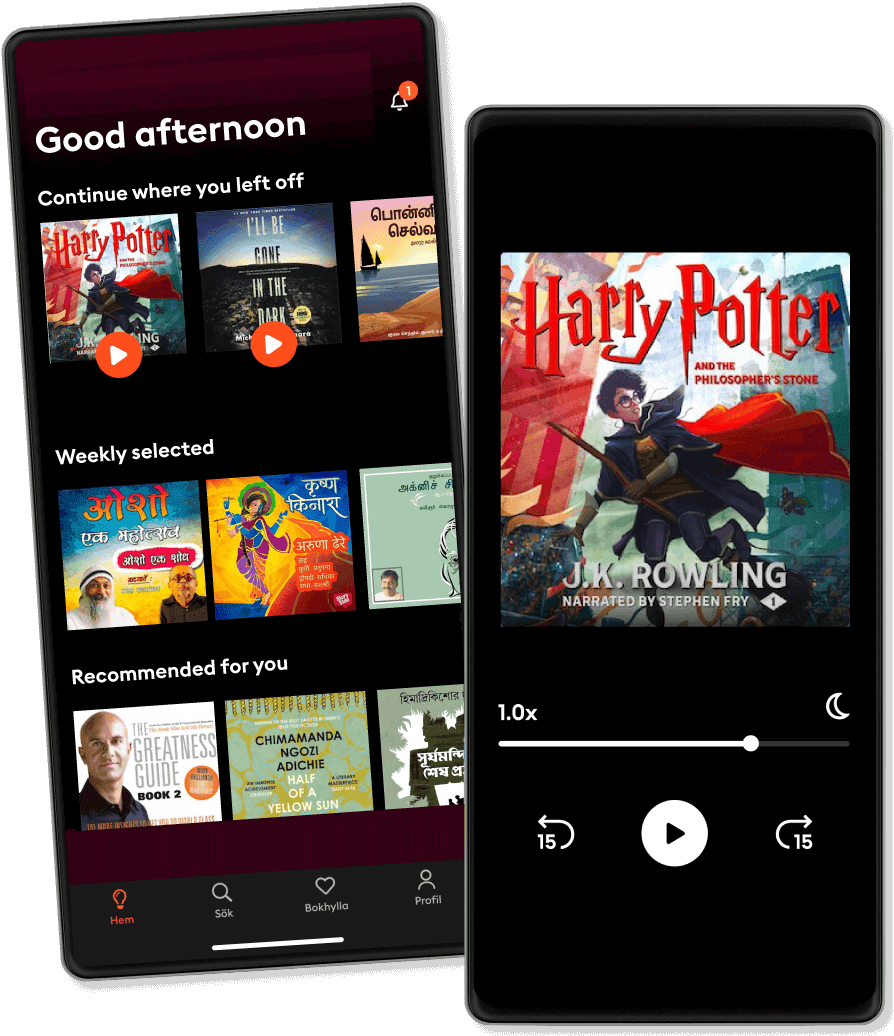
الاستماع والقراءة
خطوة إلى عالم لا حدود له من القصص
- اقرأ واستمع إلى ما تريده
- أكثر من مليون عنوان
- العناوين الحصرية + أصول القصة
- 7 يوم تجربة مجانية، ثم 34.99 ريال يورو في الشهر
- من السهل الإلغاء في أي وقت
التقييمات والاستعراضات
استعراض في لمحة
لا توجد تعليقات بعد
قم بتنزيل التطبيق للانضمام إلى المحادثة وإضافة مراجعات.
عربي
المملكة العربية السعودية