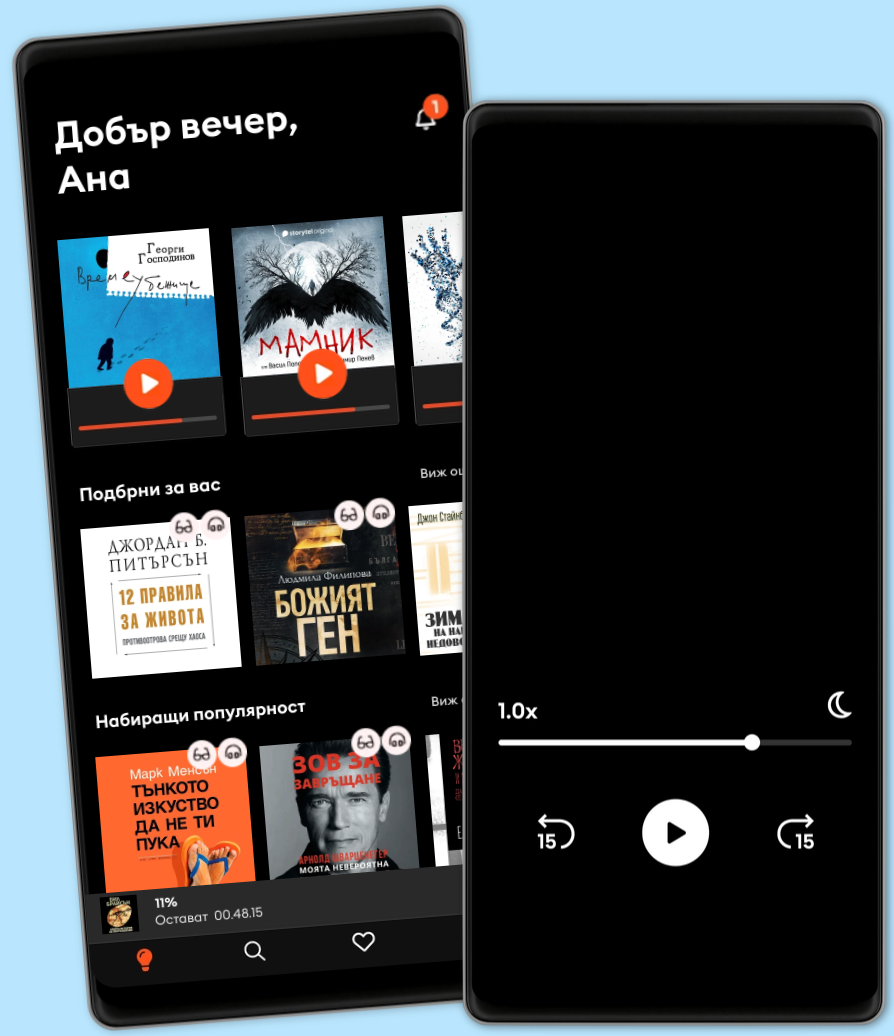
Слушайте и четете
Открийте безкрайна вселена от истории
- Слушайте и четете неограничено
- Над 500 000 заглавия
- Ексклузивни и Storytel Original заглавия
- Можете да прекратите лесно по всяко време
Metasploit Techniques and Workflows: Definitive Reference for Developers and Engineers
- От:
- Издател:
- Език
- Английски
- Format
- Категория
Документални
"Metasploit Techniques and Workflows"
"Metasploit Techniques and Workflows" is an advanced, comprehensive guide to mastering the Metasploit Framework, designed for experienced penetration testers, red teamers, and security engineers seeking to elevate their offensive security capabilities. The book begins with an in-depth exploration of Metasploit’s modular internals, revealing its architecture, core libraries, module APIs, and database integration. Readers gain hands-on insight into extending Metasploit through custom code, developing plugins, and maintaining compatibility across evolving versions—laying a technical foundation crucial for effective real-world engagements.
Building upon this expertise, the text meticulously covers each phase of the attack lifecycle. Reconnaissance workflows blend Metasploit with industry-standard tools for advanced scanning, fingerprinting, and vulnerability automation. Detailed exploitation chapters provide actionable strategies for module selection, payload management, and bypassing modern defensive mechanisms such as DEP, ASLR, and endpoint protections. Readers are equipped to engineer bespoke exploits and payloads for cross-platform operations, while post-exploitation guidance addresses privilege escalation, persistence, lateral movement, data exfiltration, and anti-forensics techniques. Rich case studies and adversary simulation frameworks ensure practical, adversary-informed understanding.
The later chapters propel professionals toward automation and large-scale operations, detailing advanced scripting, API integrations, and CI/CD pipeline utilization. Metasploit’s role in coordinated red team, purple team, and adversary simulation exercises is examined, complemented by robust coverage of detection, response, and defensive countermeasures. Forward-looking insights analyze AI augmentation, cloud and IoT exploitation trends, and evolving ethical considerations, solidifying this work as an essential reference for those driving offensive security innovation and resilience.
© 2025 HiTeX Press (Е-книга): 6610000807840
Дата на публикуване
Е-книга: 24 май 2025 г.
Разгледай още от
- Мамник - E1 Васил Попов
4.7
- Вирусът на паниката: Подкаст на Мадлен Алгафари S01E01 Мадлен Алгафари
4.9
- Хиляда сияйни слънца Халед Хосейни
4.9
- Градинарят и смъртта Георги Господинов
4.8
- Глюкозната революция Джеси Инчауспе
4.7
- Дървото на ангелите Лусинда Райли
4.8
- Ловецът на хвърчила Халед Хосейни
4.8
- Железен пламък Ребека Ярос
4.7
- Богат татко, беден татко: Актуализиран за съвременния свят и с 9 нови обучителни раздела Робърт Кийосаки
4.4
- Лейди Гергана Цветелина Цветкова
4.7
- Чук и Пук Турбьорн Егнер
4.7
- Четвърто крило Ребека Ярос
4.6
- Лехуса Васил Попов
4.6
- Четирите споразумения: Толтекска книга на мъдростта Дон Мигел Руис
4.6
- Подсъзнанието може всичко Джон Кехоу
4.7
Избери своя абонамент:
Над 500 000 заглавия
Сваляте книги за офлайн слушане
Ексклузивни заглавия + Storytel Original
Детски режим (безопасна зона за деца)
Лесно прекратявате по всяко време
Unlimited
Най-добрият избор. Открийте хиляди незабравими истории.
1 профил
Неограничен достъп
Избирайте от хиляди заглавия
Слушайте и четете неограничено
Прекратете по всяко време
Unlimited Годишен
12 месеца на цената на 8. Избирайте от хиляди заглавия.
1 профил
Неограничен достъп
9.99 лв./месец
Слушайте и четете неограничено
Прекратете по всяко време
Family
Споделете историите със семейството или приятелите си.
2-3 акаунта
Неограничен достъп
Потопете се заедно в света на историите
Слушайте и четете неограничено
Прекратете по всяко време
2 профила
21.99 лв. /30 дниБългарски
България