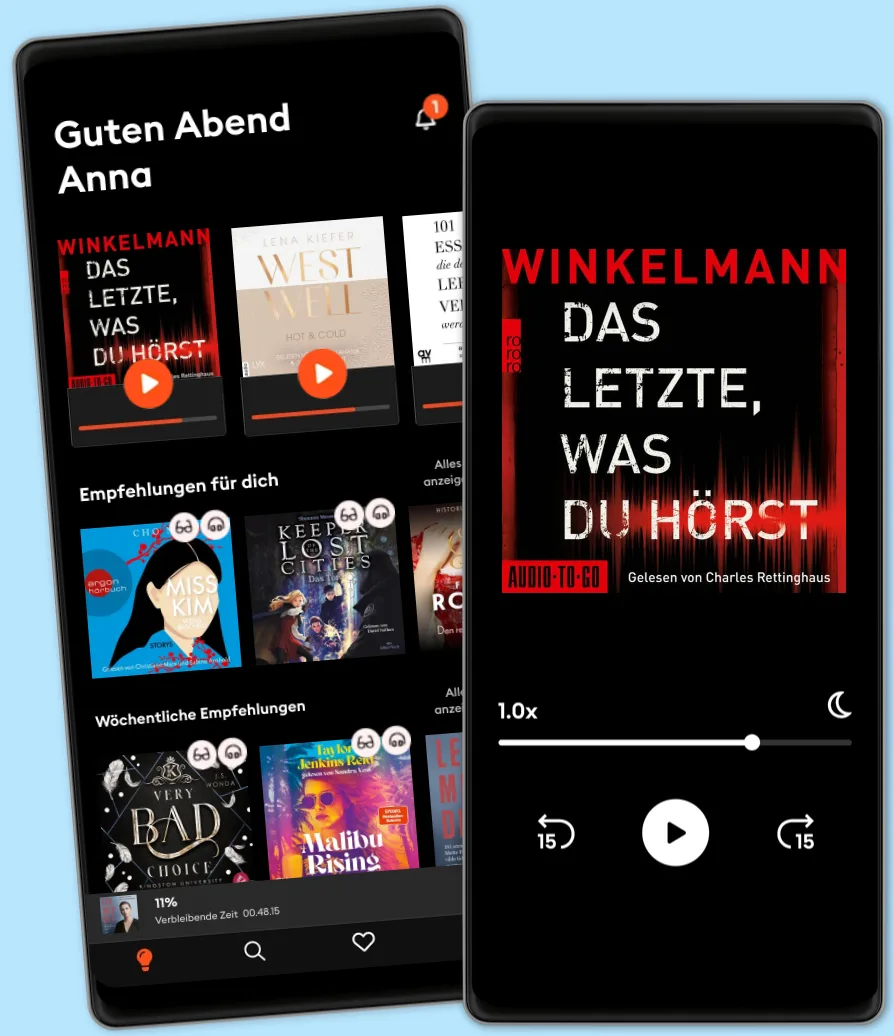
Hören und Lesen
Tritt ein in eine Welt voller Geschichten
- Mehr als 600.000 Hörbücher und E-Book
- Jederzeit kündbar
- Exklusive Titel und Originals
- komfortabler Kinder-Modus
Cybersecurity Fundamentals: How to Establish Effective Security Management Functions
- Von
- Mit:
- Verlag
Data breaches and network intrusions are constantly in front page headline news. No matter how the data was lost or the network invaded, tracing the root cause of IT security problems usually leads back to ineffective management of security programs. In this book, you'll gain solid foundational knowledge and skills you can use to effectively manage security in your organization.
You will learn:
• Objectives of Security Management • How to support Security Goals • Security Management Principles • Defense in Depth • How to apply Security Controls • Security Control Functions • How to establish Organizational Governance • Security Strategy & Governance Scenario • Information Security Relationships • Business, Compliance, and Security • Management Roles and Responsibilities • Security Roles and Responsibilities • How to create a Security Management Program • Security Management Program Structure • How to decipher the Risk Management Program • Risk Strategy Fundamentals • Risk Management Scenario • Risk within the Organization • How to conduct Risk Assessments • How to assess risk • How to respond to Risk • How to monitor Risk • Resiliency Concepts • Business Impact Analysis • Business Impact Analysis • Incident Response • Disaster Recovery • Business Continuity Fundamentals • Alternative Processing Sites • How to maintain Business Continuity
© 2020 John Knowles (Hörbuch): 9781664914308
Erscheinungsdatum
Hörbuch: 24. September 2020
Tags
Wähle dein Abo-Modell
Über 600.000 Titel
Lade Titel herunter mit dem Offline Modus
Exklusive Titel und Storytel Originals
Sicher für Kinder (Kindermodus)
Einfach jederzeit kündbar
Basic
Für alle, die gelegentlich hören und lesen.
7.90 € /Monat
Jederzeit kündbar
Abo-Upgrade jederzeit möglich
Unlimited
Für alle, die unbegrenzt hören und lesen möchten.
18.90 € /Monat
Jederzeit kündbar
Wechsel zu Basic jederzeit möglich
Anderen gefällt...
- Cybersecutity First Principles Rick Howard
- Certified Information Security Manager CISM Study Guide Mike Chapple, PhD, CISM
- Cyber Intelligence Driven Risk: How to Build, Deploy, and Use Cyber Intelligence for Improved Business Risk Decisions Richard O. Moore III
- (ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide 9th Edition Mike Chapple
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business Kim Crawley
- Web3: Charting the Internet's Next Economic and Cultural Frontier Alex Tapscott
- Cloud Security For Dummies Ted Coombs
- CompTIA Security+ All-in-One Exam Guide, Sixth Edition (Exam SY0-601) Wm. Arthur Conklin
- Building a Cyber Risk Management Program: Evolving Security for the Digital Age Brian Allen
- The Cybersecurity Playbook: How Every Leader and Employee Can Contribute to a Culture of Security Allison Cerra
- AI Ethics Mark Coeckelbergh
- The Art of Attack: Attacker Mindset for Security Professionals Maxie Reynolds
- Distrust: Big Data, Data-Torturing, and the Assault on Science Gary Smith
- How to Measure Anything in Cybersecurity Risk, 2nd Edition Douglas W. Hubbard
- Quantum Computing For Dummies whurley
- Is That a Fact?: Frauds, Quacks, and the Real Science of Everyday Life Dr. Joe Schwarcz
- Cybercrime Investigators Handbook Graeme Edwards
- 3D Printing John M. Jordan
- The Doomsday Calculation: How an Equation that Predicts the Future Is Transforming Everything We Know About Life and the Universe William Poundstone
- Trustworthy AI: A Business Guide for Navigating Trust and Ethics in AI Beena Ammanath
- The Blue Revolution: Hunting, Harvesting, and Farming Seafood in the Information Age Nicholas Sullivan
- The End of Cheap China: Economic and Cultural Trends That Will Disrupt the World Shaun Rein
- Haptics Lynette Jones
- The Aisles Have Eyes: How Retailers Track Your Shopping, Strip Your Privacy, and Define Your Power Joseph Turow
- How Big-Tech Barons Smash Innovation—and How to Strike Back Maurice E. Stucke
- CISSP All-in-One Exam Guide, Ninth Edition Fernando Maymi
- Behavioural Economics: Psychology, neuroscience, and the human side of economics David Orrell
- Preventing the Next Pandemic: Vaccine Diplomacy in a Time of Anti-science Peter J. Hotez
- Business Ethics for Better Behavior Jason Brennan
- The New Roaring Twenties: Prosper in Volatile Times Paul Zane Pilzer
- The Road to Reinvention: How to Drive Disruption and Accelerate Transformation Josh Linkner
- Catching Up to Crypto: Your Guide to Bitcoin and the New Digital Economy Ben Armstrong
- Cybersecurity For Dummies Joseph Steinberg
- Billionaires in World Politics Peter Hagel
- Disrupting Sacred Cows Garrett Gunderson
- The Vanishing American Corporation: Navigating the Hazards of a New Economy Gerald F. Davis
- The Legal Analyst: A Toolkit for Thinking about the Law Ward Farnsworth
- The Great Persuasion: Reinventing Free Markets Since the Depression Angus Burgin
- Ethical Machines: Your Concise Guide to Totally Unbiased, Transparent, and Respectful AI Reid Blackman
- Thinking Like an Economist: How Efficiency Replaced Equality in U.S. Public Policy Elizabeth Popp Berman
- Auto Repair For Dummies: 2nd Edition Deanna Sclar
- A Leader’s Guide to Cybersecurity: Why Boards Need to Lead-And How to Do It Jack J. Domet
- Fake Photos Hany Farid
- The New Technology Elite: How Great Companies Optimize Both Technology Consumption and Production Vinnie Mirchandani
- The DevSecOps Playbook: Deliver Continuous Security at Speed Sean D. Mack
- Age of Invisible Machines: A Practical Guide to Creating a Hyperautomated Ecosystem of Intelligent Digital Workers Robb Wilson
- Maxims for Thinking Analytically: The Wisdom of Legendary Harvard Professor Richard Zeckhauser Dan Levy
- Trading at the Speed of Light: How Ultrafast Algorithms Are Transforming Financial Markets Donald MacKenzie
- Fourth Wing – Flammengeküsst (Flammengeküsst-Reihe 1) Rebecca Yarros
4.7
- Iron Flame – Flammengeküsst (Flammengeküsst-Reihe 2): Die heißersehnte Fortsetzung des Fantasy-Erfolgs »Fourth Wing« Rebecca Yarros
4.7
- Rubinrot - Liebe geht durch alle Zeiten - Liebe geht durch alle Zeiten. Die Edelstein-Trilogie, Band 1 (Ungekürzte Lesung) Kerstin Gier
4.6
- Onyx Storm – Flammengeküsst (Flammengeküsst-Reihe 3): Die heißersehnte Fortsetzung von »Fourth Wing« und »Iron Flame« Rebecca Yarros
4.3
- The Paradise Problem – Wenn das Herz den perfekten Plan durchkreuzt: Nach »The Unhoneymooners« endlich die neue paradiesisch prickelnde RomCom der SPIEGEL-Bestsellerautorin Christina Lauren
4.4
- The Wrong Bride - The Windsors, Teil 1 (Ungekürzt) Catharina Maura
4.3
- Not Quite Dead Yet (Ungekürzt) Holly Jackson
4.6
- The Pumpkin Spice Latte Disaster (Lower Whilby 1): In dieser cosy RomCom treffen Stars Hollow-Vibes auf die Enemies to lover-Trope Kyra Groh
4.4
- Just for the Summer Abby Jimenez
4.5
- "Mama, bitte lern Deutsch" - Unser Eingliederungsversuch in eine geschlossene Gesellschaft (Ungekürzte Autorenlesung) Tahsim Durgun
4.8
- Der dunkle Sommer (Ungekürzte Lesung) Vera Buck
4.7
- Alchemised: Das internationale Phänomen – jetzt auch als Hörbuch SenLinYu
4.3
- Throne of Glass 1: Die Erwählte Sarah J. Maas
4.6
- Boys of Tommen 5: Taming 7: Die BookTok-Sensation endlich auf Deutsch Chloe Walsh
4.8
- 22 Bahnen: Lieblingsbuch des unabhängigen Buchhandels 2023 Caroline Wahl
4.1
Deutsch
Deutschland