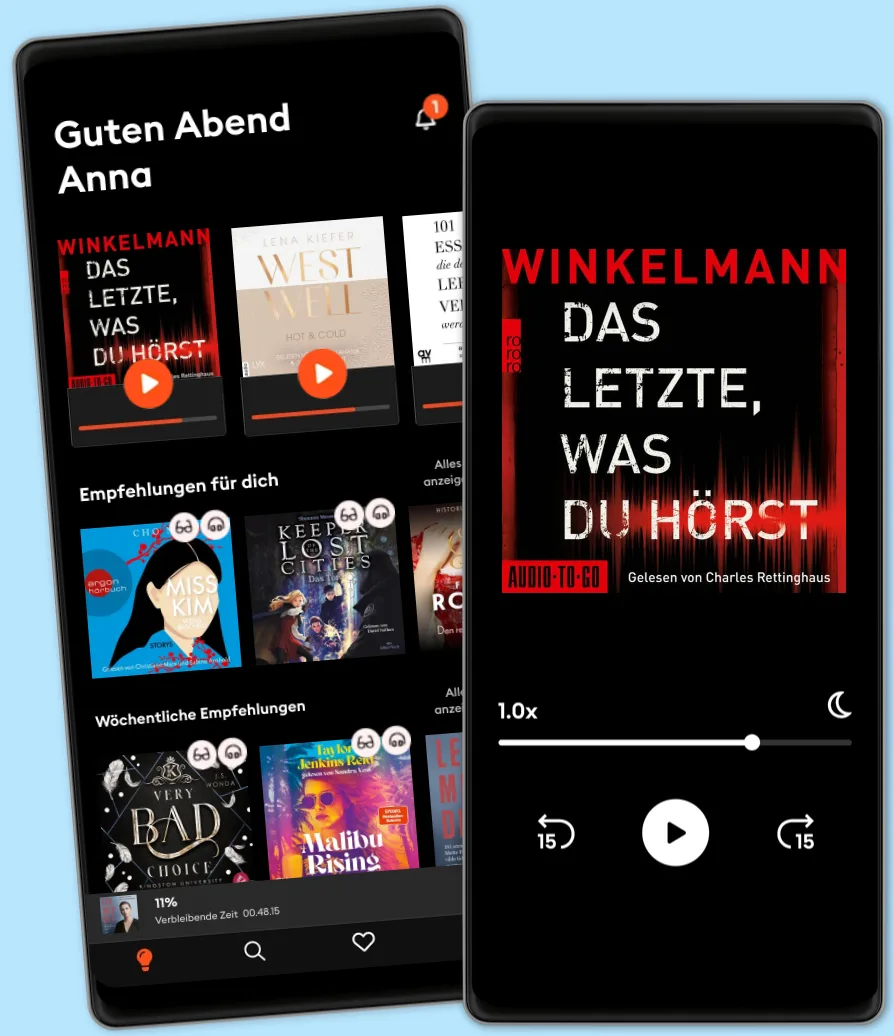
Hören und Lesen
Tritt ein in eine Welt voller Geschichten
- Mehr als 600.000 Hörbücher und E-Book
- Jederzeit kündbar
- Exklusive Titel und Originals
- komfortabler Kinder-Modus
ETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking world
- Von
- Verlag
- Sprachen
- Englisch
- Format
- Kategorie
Sachbuch
Ethical hacking, also known as penetration testing or white-hat hacking, is a practice of deliberately probing and assessing the security of computer systems, networks, applications, and other digital environments in order to identify vulnerabilities and weaknesses that could potentially be exploited by malicious hackers. The primary goal of ethical hacking is to proactively uncover these vulnerabilities before they can be exploited by unauthorized individuals or groups, thereby helping organizations strengthen their security measures and protect their sensitive information. Key aspects of ethical hacking include: Authorization: Ethical hackers must obtain proper authorization from the owner or administrator of the system before conducting any tests. This ensures that the testing process remains within legal and ethical boundaries. Methodology: Ethical hacking involves a systematic and structured approach to identify vulnerabilities. This includes various techniques like network scanning, penetration testing, social engineering, and vulnerability assessment. Scope: The scope of an ethical hacking engagement is defined before the testing begins. It outlines the systems, applications, and networks that will be tested. Staying within the defined scope ensures that only authorized systems are tested. Information Gathering: Ethical hackers gather information about the target systems, including their architecture, software versions, and potential weak points. This information helps them plan their testing approach. Vulnerability Analysis: Ethical hackers use various tools and techniques to identify vulnerabilities, misconfigurations, and weak points in the target systems. These vulnerabilities could include software bugs, insecure configurations, or design flaws. Exploitation: In a controlled environment, ethical hackers might attempt to exploit the identified vulnerabilities to demonstrate the potential impact of a real attack. However, they stop short of causing
© 2023 BookRix (E-Book): 9783755451433
Erscheinungsdatum
E-Book: 29. August 2023
Tags
Wähle dein Abo-Modell
Über 600.000 Titel
Lade Titel herunter mit dem Offline Modus
Exklusive Titel und Storytel Originals
Sicher für Kinder (Kindermodus)
Einfach jederzeit kündbar
Basic
Für alle, die gelegentlich hören und lesen.
7.90 € /Monat
Jederzeit kündbar
Abo-Upgrade jederzeit möglich
Unlimited
Für alle, die unbegrenzt hören und lesen möchten.
18.90 € /Monat
Jederzeit kündbar
Wechsel zu Basic jederzeit möglich
- Fourth Wing – Flammengeküsst (Flammengeküsst-Reihe 1) Rebecca Yarros
4.7
- Iron Flame – Flammengeküsst (Flammengeküsst-Reihe 2): Die heißersehnte Fortsetzung des Fantasy-Erfolgs »Fourth Wing« Rebecca Yarros
4.7
- Rubinrot - Liebe geht durch alle Zeiten - Liebe geht durch alle Zeiten. Die Edelstein-Trilogie, Band 1 (Ungekürzte Lesung) Kerstin Gier
4.6
- Onyx Storm – Flammengeküsst (Flammengeküsst-Reihe 3): Die heißersehnte Fortsetzung von »Fourth Wing« und »Iron Flame« Rebecca Yarros
4.3
- The Paradise Problem – Wenn das Herz den perfekten Plan durchkreuzt: Nach »The Unhoneymooners« endlich die neue paradiesisch prickelnde RomCom der SPIEGEL-Bestsellerautorin Christina Lauren
4.4
- The Wrong Bride - The Windsors, Teil 1 (Ungekürzt) Catharina Maura
4.3
- Not Quite Dead Yet (Ungekürzt) Holly Jackson
4.6
- The Pumpkin Spice Latte Disaster (Lower Whilby 1): In dieser cosy RomCom treffen Stars Hollow-Vibes auf die Enemies to lover-Trope Kyra Groh
4.4
- Just for the Summer Abby Jimenez
4.5
- "Mama, bitte lern Deutsch" - Unser Eingliederungsversuch in eine geschlossene Gesellschaft (Ungekürzte Autorenlesung) Tahsim Durgun
4.8
- Der dunkle Sommer (Ungekürzte Lesung) Vera Buck
4.7
- Alchemised: Das internationale Phänomen – jetzt auch als Hörbuch SenLinYu
4.3
- Throne of Glass 1: Die Erwählte Sarah J. Maas
4.6
- Boys of Tommen 5: Taming 7: Die BookTok-Sensation endlich auf Deutsch Chloe Walsh
4.8
- 22 Bahnen: Lieblingsbuch des unabhängigen Buchhandels 2023 Caroline Wahl
4.1
Deutsch
Deutschland