Building Effective Cybersecurity Programs: A Security Manager’s Handbook
- Por
- Editor
- Colecciones
1 de 13
- Idioma
- Inglés
- Formato
- Categoría
Economía y negocios
You know by now that your company could not survive without the Internet. Not in today’s market. You are either part of the digital economy or reliant upon it. With critical information assets at risk, your company requires a state-of-the-art cybersecurity program. But how do you achieve the best possible program? Tari Schreider, in Building Effective Cybersecurity Programs: A Security Manager’s Handbook, lays out the step-by-step roadmap to follow as you build or enhance your cybersecurity program.
Over 30+ years, Tari Schreider has designed and implemented cybersecurity programs throughout the world, helping hundreds of companies like yours. Building on that experience, he has created a clear roadmap that will allow the process to go more smoothly for you. Building Effective Cybersecurity Programs: A Security Manager’s Handbook is organized around the six main steps on the roadmap that will put your cybersecurity program in place:
1. Design a Cybersecurity Program 2. Establish a Foundation of Governance 3. Build a Threat, Vulnerability Detection, and Intelligence Capability 4. Build a Cyber Risk Management Capability 5. Implement a Defense-in-Depth Strategy 6. Apply Service Management to Cybersecurity Programs
Because Schreider has researched and analyzed over 150 cybersecurity architectures, frameworks, and models, he has saved you hundreds of hours of research. He sets you up for success by talking to you directly as a friend and colleague, using practical examples. His book helps you to:
• Identify the proper cybersecurity program roles and responsibilities. • Classify assets and identify vulnerabilities. • Define an effective cybersecurity governance foundation. • Evaluate the top governance frameworks and models. • Automate your governance program to make it more effective. • Integrate security into your application development process. • Apply defense-in-depth as a multi-dimensional strategy. • Implement a service management approach to implementing countermeasures.
With this handbook, you can move forward confidently, trusting that Schreider is recommending the best components of a cybersecurity program for you. In addition, the book provides hundreds of citations and references allow you to dig deeper as you explore specific topics relevant to your organization or your studies.
© 2017 Rothstein Publishing (Libro electrónico): 9781944480509
Fecha de lanzamiento
Libro electrónico: 20 de octubre de 2017
Otros también disfrutaron ...
- La mala hija Pedro Martí
- Comerás flores Lucía Solla Sobral
- Llevará tu nombre Sonsoles Ónega
- Las gratitudes Delphine de Vigan
- Maite Fernando Aramburu
- Momentos oscuros Elisa Hoven
- El método Elisa Mamen de Blas
- La intriga del funeral inconveniente Eduardo Mendoza
- La novia gitana (Inspectora Elena Blanco 1) Carmen Mola
- Con amor, mamá: El thriller más viral del año, que se ha convertido en un fenómeno global Iliana Xander
- Hasta que te quedes Manuel Marlasca
- La sombra del loto negro: Premio Minotauro 2026 África Vázquez Beltrán
- El arte de mentir - ¿Té? ¿Café? ¡Misterio!, Episodio 1 (Íntegro) Ellen Barksdale
- Tú bailas y yo disparo: Serie Grupo X 1 Manuel Marlasca
- Los amores paralelos Mayte Uceda
Elige el plan:
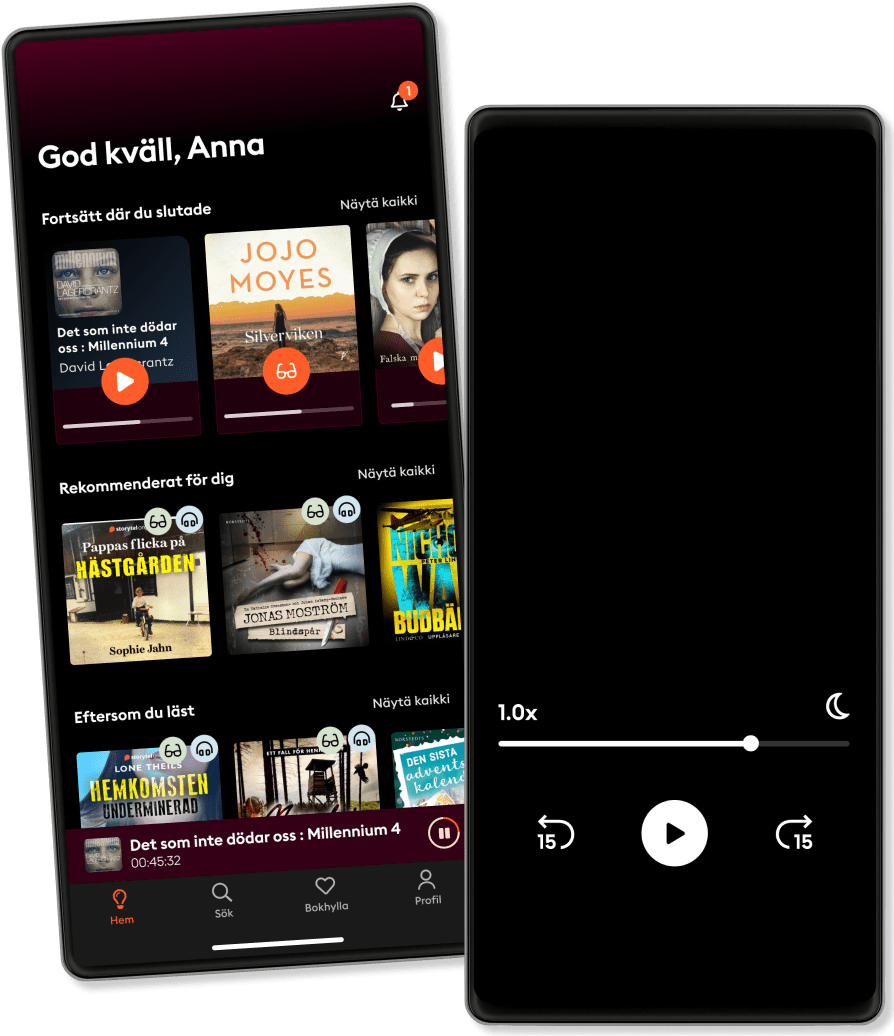
Más de 650.000 títulos
Kids mode
Modo sin conexión
Cancela cuando quieras
Unlimited
Nada mejor que 90 días de audiolibros gratis.
8.99 € /mes
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
Family
Para los que quieren compartir historias con su familia y amigos.
Desde 15.99 € /mes
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
15.99 € /mes