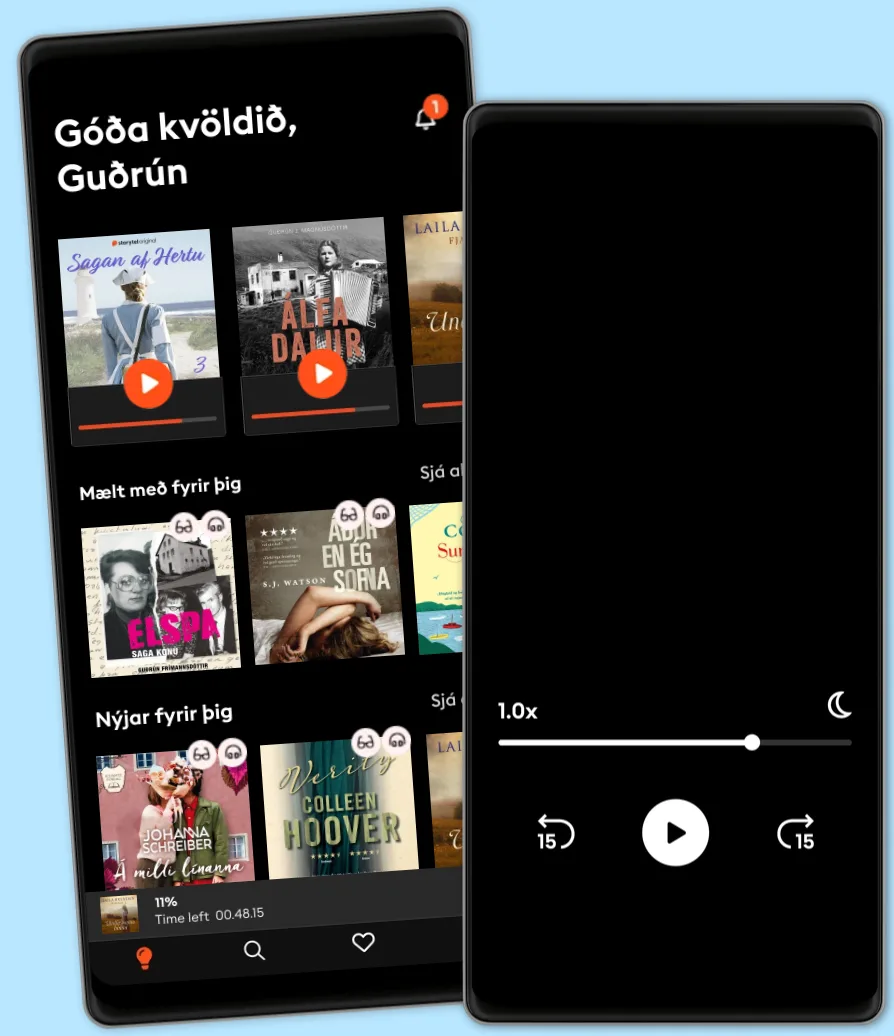
Hlustaðu og lestu
Stígðu inn í heim af óteljandi sögum
- Lestu og hlustaðu eins mikið og þú vilt
- Þúsundir titla
- Getur sagt upp hvenær sem er
- Engin skuldbinding
Effective Threat Investigation for SOC Analysts: The ultimate guide to examining various threats and attacker techniques using security logs
- Eftir
- Útgefandi
- Tungumál
- enska
- Snið
- Bókaflokkur
Óskáldað efni
Effective threat investigation requires strong technical expertise, analytical skills, and a deep understanding of cyber threats and attacker techniques. It's a crucial skill for SOC analysts, enabling them to analyze different threats and identify security incident origins. This book provides insights into the most common cyber threats and various attacker techniques to help you hone your incident investigation skills. The book begins by explaining phishing and email attack types and how to detect and investigate them, along with Microsoft log types such as Security, System, PowerShell, and their events. Next, you’ll learn how to detect and investigate attackers' techniques and malicious activities within Windows environments. As you make progress, you’ll find out how to analyze the firewalls, flows, and proxy logs, as well as detect and investigate cyber threats using various security solution alerts, including EDR, IPS, and IDS. You’ll also explore popular threat intelligence platforms such as VirusTotal, AbuseIPDB, and X-Force for investigating cyber threats and successfully build your own sandbox environment for effective malware analysis. By the end of this book, you’ll have learned how to analyze popular systems and security appliance logs that exist in any environment and explore various attackers' techniques to detect and investigate them with ease.
© 2023 Packt Publishing (Rafbók): 9781837638758
Útgáfudagur
Rafbók: 25 augusti 2023
Merki
- Sálarstríð Steindór Ívarsson
4.6
- Hennar hinsta stund Carla Kovach
4.1
- Skilnaðurinn Moa Herngren
4
- Fiðrildaherbergið Lucinda Riley
4.4
- Hvarfið Torill Thorup
4.4
- Kvöldið sem hún hvarf Eva Björg Ægisdóttir
4.3
- Dökkir skuggar Laila Brenden
4.4
- Franska sveitabýlið Jo Thomas
4
- Myrká Arnaldur Indriðason
4.4
- Hildur Satu Rämö
4.3
- Vinkonur að eilífu? Sarah Morgan
4.1
- Litla leynivíkin í Króatíu Julie Caplin
4.2
- Aldrei aldrei Colleen Hoover
3.1
- Ég læt sem ég sofi Yrsa Sigurðardóttir
4.1
- Fjölskyldudeilan Torill Thorup
4.4
Veldu áskrift
Yfir 900.000 hljóð- og rafbækur
Yfir 400 titlar frá Storytel Original
Barnvænt viðmót með Kids Mode
Vistaðu bækurnar fyrir ferðalögin
Unlimited
Besti valkosturinn fyrir einn notanda
3290 kr /mánuði
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
Family
Fyrir þau sem vilja deila sögum með fjölskyldu og vinum.
Byrjar á 3990 kr /mánuður
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
3990 kr /mánuði
Íslenska
Ísland