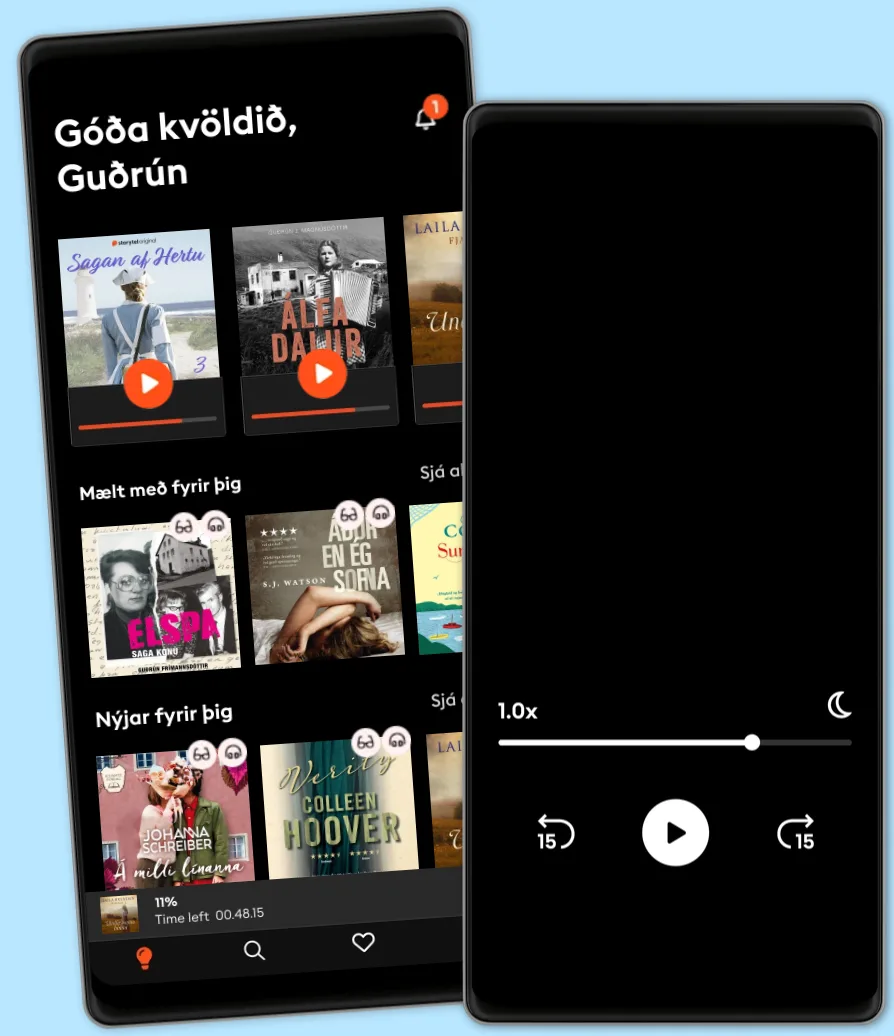
Hlustaðu og lestu
Stígðu inn í heim af óteljandi sögum
- Lestu og hlustaðu eins mikið og þú vilt
- Þúsundir titla
- Getur sagt upp hvenær sem er
- Engin skuldbinding
Zero Trust Networks: Building Secure Systems in Untrusted Networks (2nd Edition)
- Eftir
- Með:
- Útgefandi
- Lengd
- 12 Klst. 5 mín.
- Tungumál
- enska
- Snið
- Bókaflokkur
Óskáldað efni
Perimeter defenses guarding your network aren't as secure as you might think. Hosts behind the firewall have no defenses of their own, so when a host in the "trusted" zone is breached, access to your data center is not far behind. This practical book introduces you to the zero trust model, a method that treats all hosts as if they're internet-facing, and considers the entire network to be compromised and hostile.
In this updated edition, the authors show you how zero trust lets you focus on building strong authentication, authorization, and encryption throughout, while providing compartmentalized access and better operational agility. You'll learn the architecture of a zero trust network, including how to build one using currently available technology.
You'll also explore fundamental concepts of a zero trust network, including trust engine, policy engine, and context aware agents; discover how this model embeds security within the system's operation, rather than layering it on top; use existing technology to establish trust among the actors in a network; migrate from a perimeter-based network to a zero trust network in production; examine case studies that provide insights into various organizations' zero trust journeys; and learn about the various zero trust architectures, standards, and frameworks.
© 2024 Ascent Audio (Hljóðbók): 9781663735584
Útgáfudagur
Hljóðbók: 4 juni 2024
Merki
Aðrir höfðu einnig áhuga á...
- Learning DevSecOps: A Practical Guide to Processes and Tools Steve Suehring
- Artificial Integrity: The Paths to Leading AI Toward a Human-Centered Future Hamilton Mann
- Ben Hardy’s Flying Machine: The Power of Imagination Frank Webster
- Unique Selections: Twelve Sci-Fi Classic Stories H. G. Wells
- Aggressor: The Aggressor Series Book 1 F X Holden
- Swimming Pretty: The Untold Story of Women in Water Vicki Valosik
- Literary Theory for Robots: How Computers Learned to Write Dennis Yi Tenen
- The Wheels of Chance: A Bicycling Idyll H. G. Wells
- Hennar hinsta stund Carla Kovach
4.1
- Sálarstríð Steindór Ívarsson
4.6
- Skilnaðurinn Moa Herngren
4
- Hvarfið Torill Thorup
4.4
- Fiðrildaherbergið Lucinda Riley
4.4
- Kvöldið sem hún hvarf Eva Björg Ægisdóttir
4.3
- Dökkir skuggar Laila Brenden
4.4
- Franska sveitabýlið Jo Thomas
4
- Myrká Arnaldur Indriðason
4.4
- Hildur Satu Rämö
4.3
- Vinkonur að eilífu? Sarah Morgan
4.1
- Aldrei aldrei Colleen Hoover
3.1
- Áttunda fórnarlambið Birgitta H. Halldórsdóttir
4
- Litla leynivíkin í Króatíu Julie Caplin
4.2
- Ég læt sem ég sofi Yrsa Sigurðardóttir
4.1
Veldu áskrift
Yfir 900.000 hljóð- og rafbækur
Yfir 400 titlar frá Storytel Original
Barnvænt viðmót með Kids Mode
Vistaðu bækurnar fyrir ferðalögin
Unlimited
Besti valkosturinn fyrir einn notanda
3290 kr /mánuði
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
Family
Fyrir þau sem vilja deila sögum með fjölskyldu og vinum.
Byrjar á 3990 kr /mánuður
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
3990 kr /mánuði
Íslenska
Ísland