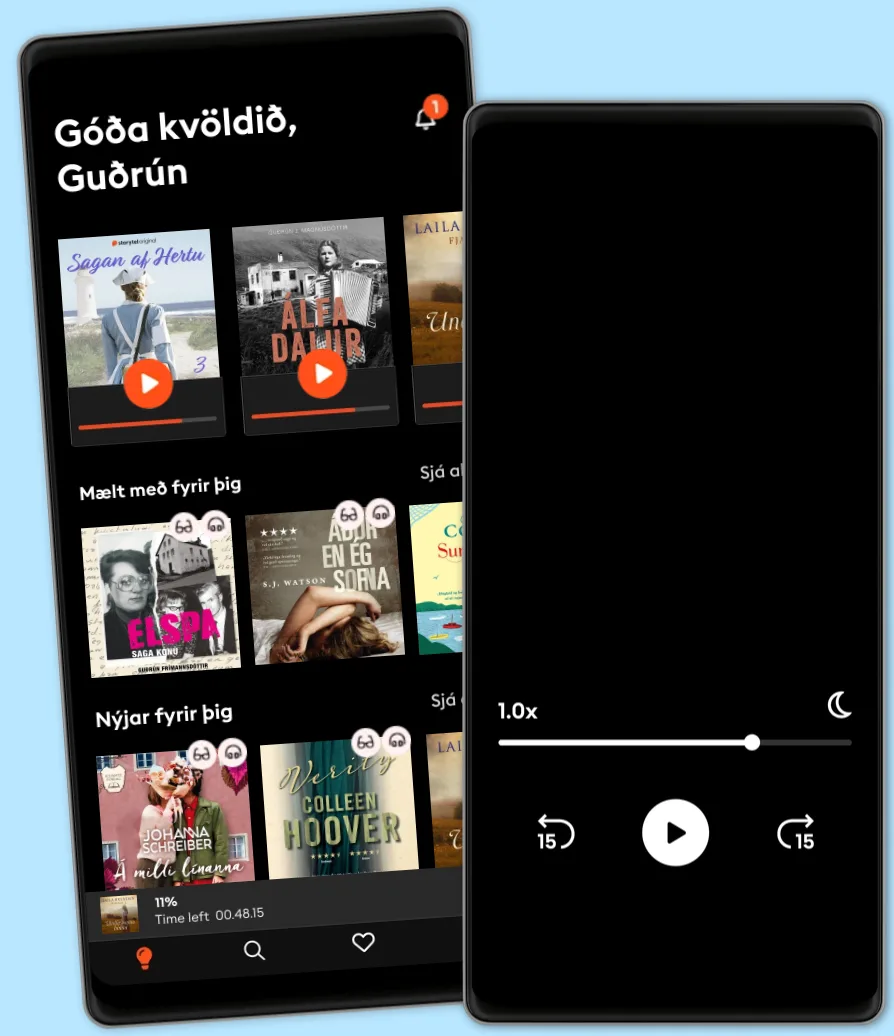
Hlustaðu og lestu
Stígðu inn í heim af óteljandi sögum
- Lestu og hlustaðu eins mikið og þú vilt
- Þúsundir titla
- Getur sagt upp hvenær sem er
- Engin skuldbinding
OAuth 2.0 Cookbook: Protect your web applications using Spring Security
- Eftir
- Útgefandi
- Tungumál
- enska
- Snið
- Bókaflokkur
Óskáldað efni
Efficiently integrate OAuth 2.0 to protect your mobile, desktop, Cloud applications and APIs using Spring Security technologies.
About This Book • Interact with public OAuth 2.0 protected APIs such as Facebook, LinkedIn and Google.
• Use Spring Security and Spring Security OAuth2 to implement your own OAuth 2.0 provider
• Learn how to implement OAuth 2.0 native mobile clients for Android applications
Who This Book Is For
This book targets software engineers and security experts who are looking to develop their skills in API security and OAuth 2.0. Prior programming knowledge and a basic understanding of developing web applications are necessary. As this book's recipes mostly use Spring Security and Spring Security OAuth2, some prior experience with Spring Framework will be helpful.
What You Will Learn • Use Redis and relational databases to store issued access tokens and refresh tokens
• Access resources protected by the OAuth2 Provider using Spring Security
• Implement a web application that dynamically registers itself to the Authorization Server
• Improve the safety of your mobile client using dynamic client registration
• Protect your Android client with Proof Key for Code Exchange
• Protect the Authorization Server from invalid redirection
In Detail
OAuth 2.0 is a standard protocol for authorization and focuses on client development simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and so on. This book also provides useful recipes for solving real-life problems using Spring Security and creating Android applications.
The book starts by presenting you how to interact with some public OAuth 2.0 protected APIs such as Facebook, LinkedIn and Google. You will also be able to implement your own OAuth 2.0 provider with Spring Security OAuth2. Next, the book will cover practical scenarios regarding some important OAuth 2.0 profiles such as Dynamic Client Registration, Token Introspection and how to revoke issued access tokens. You will then be introduced to the usage of JWT, OpenID Connect, and how to safely implement native mobile OAuth 2.0 Clients.
By the end of this book, you will be able to ensure that both the server and client are protected against common vulnerabilities.
Style and approach
With the help of real-world examples, this book provides step by step recipes for troubleshooting and extending your API security. The book also helps you with accessing and securing data on mobile, desktop, and cloud apps with OAuth 2.0.
© 2017 Packt Publishing (Rafbók): 9781788290630
Útgáfudagur
Rafbók: 18 oktober 2017
Merki
Aðrir höfðu einnig áhuga á...
- Sálarstríð Steindór Ívarsson
4.6
- Kvöldið sem hún hvarf Eva Björg Ægisdóttir
4.3
- Hennar hinsta stund Carla Kovach
4.1
- Litla leynivíkin í Króatíu Julie Caplin
4.2
- Fiðrildaherbergið Lucinda Riley
4.4
- Fjölskyldudeilan Torill Thorup
4.4
- Dökkir skuggar Laila Brenden
4.4
- Skilnaðurinn Moa Herngren
4
- Ég læt sem ég sofi Yrsa Sigurðardóttir
4.1
- Klækir Kamelljónsins Birgitta H. Halldórsdóttir
4.1
- Hægri höndin Mohlin & Nyström
4.2
- Hvarfið Torill Thorup
4.4
- Franska sveitabýlið Jo Thomas
4
- Hildur Satu Rämö
4.3
- Myrká Arnaldur Indriðason
4.4
Veldu áskrift
Yfir 900.000 hljóð- og rafbækur
Yfir 400 titlar frá Storytel Original
Barnvænt viðmót með Kids Mode
Vistaðu bækurnar fyrir ferðalögin
Hlustaðu og lestu á sama tíma
Unlimited
Besti valkosturinn fyrir einn notanda
3290 kr /mánuði
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
Family
Fyrir þau sem vilja deila sögum með fjölskyldu og vinum.
Byrjar á 3990 kr /mánuður
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
3990 kr /mánuði
Íslenska
Ísland