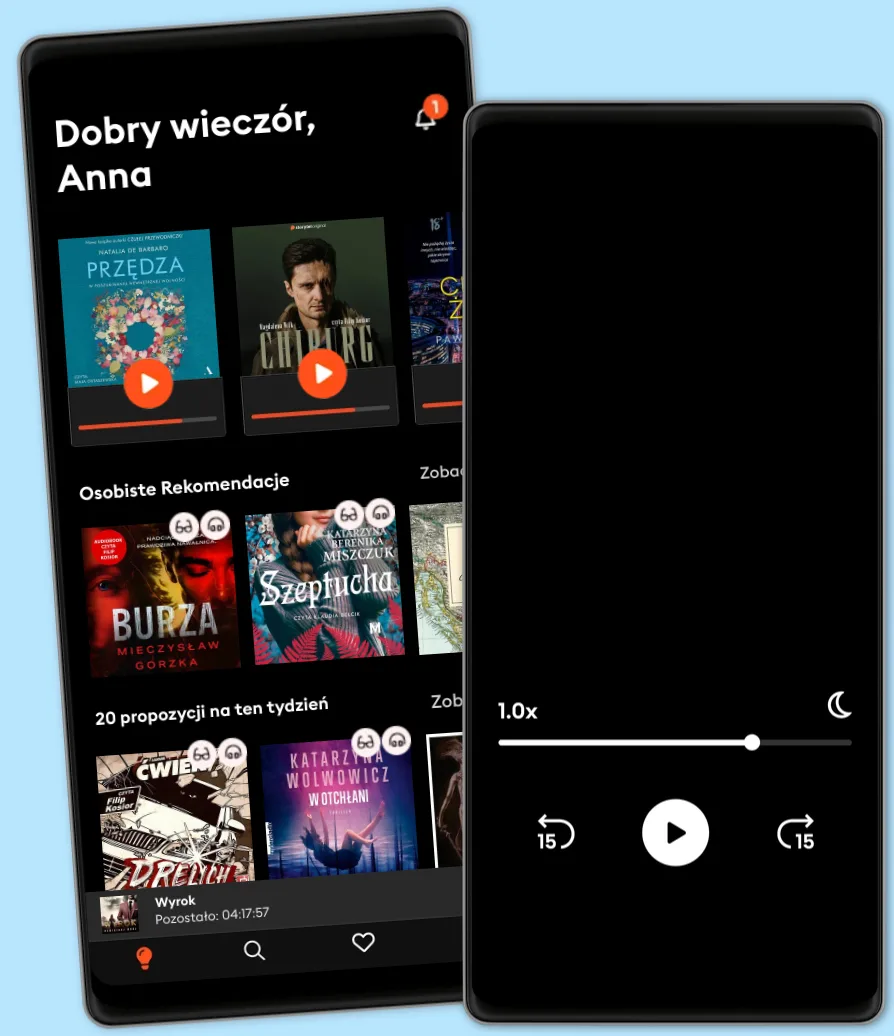
Słuchaj i czytaj 50% taniej przez 4 miesiące!
Znajdź swoją nową ulubioną historię - teraz za jedyne 19,95 zł miesięcznie przez pierwsze 4 miesiące
- Czytaj i słuchaj jak chcesz i ile chcesz
- Ponad 500 000 tytułów
- Tytuły dostępne wyłącznie w Storytel oraz Storytel Originals
- Łatwa rezygnacja w dowolnym momencie
Learn Social Engineering: Learn the art of human hacking with an internationally renowned expert
- Autor
- Wydawca
- Język
- Angielski
- Format
- Kategoria
Literatura Faktu
Improve information security by learning Social Engineering.
Key Features • Learn to implement information security using social engineering
• Get hands-on experience of using different tools such as Kali Linux, the Social Engineering toolkit and so on
• Practical approach towards learning social engineering, for IT security
Book Description
This book will provide you with a holistic understanding of social engineering. It will help you to avoid and combat social engineering attacks by giving you a detailed insight into how a social engineer operates.
Learn Social Engineering starts by giving you a grounding in the different types of social engineering attacks, and the damages they cause. It then sets up the lab environment to use different toolS and then perform social engineering steps such as information gathering. The book covers topics from baiting, phishing, and spear phishing, to pretexting and scareware.
By the end of the book, you will be in a position to protect yourself and
your systems from social engineering threats and attacks.
All in all, the book covers social engineering from A to Z , along with excerpts from many world wide known security experts.
What you will learn • Learn to implement information security using social engineering
• Learn social engineering for IT security
• Understand the role of social media in social engineering
• Get acquainted with Practical Human hacking skills
• Learn to think like a social engineer
• Learn to beat a social engineer
Who this book is for
This book targets security professionals, security analysts, penetration testers, or any stakeholder working with information security who wants to learn how to use social engineering techniques. Prior knowledge of Kali Linux is an added advantage
Dr. Erdal Ozkaya is a doctor of IT in cybersecurity and master of information systems security. He holds many industry certifications, such as CEI, MCT, MCSE, E|CEH, E|CISO, CFR, and CISSP. He works for Microsoft as a cybersecurity architect and security advisor, and he is also a part-time lecturer at Charles Sturt University. He has coauthored many cybersecurity books and security certification courseware for different vendors. He speaks at worldwide conferences. He has won many awards in his field, and he works hard to make the cyberworld safe.
© 2018 Packt Publishing (E-book): 9781788838009
Wydanie
E-book: 30 kwietnia 2018
Tagi
Inni polubili także ...
- The Dark Science Of Psychological Warfare: How To Always Keep The Upper Hand On Anyone Psychologically Madison Taylor
- Ham Radio Handbook: Baofeng Basics for Beginners Nathan Venture, D
- A Degree in a Book: Electrical And Mechanical Engineering: Everything You Need to Know to Master the Subject - in One Book! David Baker
- Motivational Interviewing 101: An All-Encompassing Comprehensive Guide on the Most Effective Methods for Practitioners Scientia Media Group
- Start Telling People: The guide to marketing strategy and brand building for future-defining startups Chris Matthews
- Blood Evidence Grace Campbell
- The Art Of Deception: How To Master And Use Subterfuge On Anyone Madison Taylor
- Ham Radio For Dummies: 4th Edition H. Ward Silver
- Leadership Two Words at a Time: Simple Truths for Leading Complicated People Bill Treasurer
- Evolutionary Intelligence: How Technology Will Make Us Smarter W. Russell Neuman
- Avatar-Philosophy (and -Religion) or FAITHEISM Edmond Wright
- Wieża jaskółki Andrzej Sapkowski
4.9
- Harry Potter i Kamień Filozoficzny J.K. Rowling
4.7
- Zła przeszłość Mieczysław Gorzka
4.8
- Kasprowy Remigiusz Mróz
4.5
- Harry Potter i Komnata Tajemnic J.K. Rowling
4.8
- Zło Katarzyna Wolwowicz
4.8
- Wolta Dariusz Gizak
4.7
- Wiedźmin Andrzej Sapkowski
4.7
- Wilczyca Mieczysław Gorzka
4.6
- Harry Potter i Więzień Azkabanu J.K. Rowling
4.8
- Gra o tron George R.R. Martin
4.9
- Krew elfów Andrzej Sapkowski
4.8
- Pierwsza sprawa. Komisarz Oczko (1) Tomasz Wandzel
4.3
- Tajemnicze jajo Pamela Butchart
4.3
- Szczęścia można się nauczyć Ewa Woydyłło
4.8
Wybierz swoją subskrypcję:
Ponad 500 000 tytułów w cenie jednego abonamentu
Słuchaj i czytaj w trybie offline
Ekskluzywne produkcje audio Storytel Original
Tryb dziecięcy Kids Mode
Anuluj kiedy chcesz
Unlimited
Dla tych, którzy chcą słuchać i czytać bez limitów.
1 konto
Nielimitowany Dostęp
1 konto
Słuchanie bez limitów
Anuluj w dowolnym momencie
Unlimited na rok
Dla tych, którzy chcą słuchać i czytać bez limitów.
1 konto
Nielimitowany Dostęp
1 konto
Słuchanie bez limitów
Anuluj w dowolnym momencie
Basic
Dla tych, którzy słuchają i czytają od czasu do czasu.
1 konto
10 godzin/miesięcznie
1 konto
10 godzin / miesiąc
Anuluj w dowolnym momencie
Family
Dla tych, którzy chcą dzielić się historiami ze znajomymi i rodziną.
2-3 kont
Nielimitowany Dostęp
2–3 konta
Słuchanie bez limitów
Anuluj w dowolnym momencie
2 konta
59.90 zł /30 dniPolski
Polska