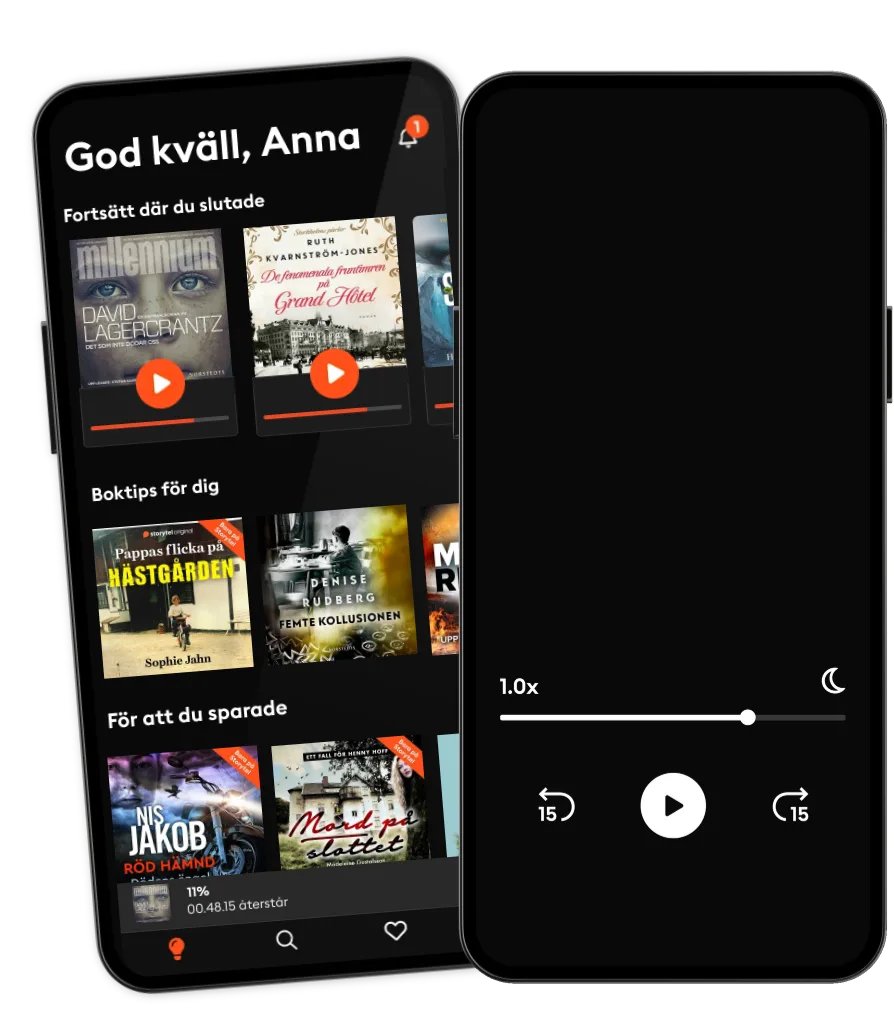
Lyssna när som helst, var som helst
Kliv in i en oändlig värld av stories
- 1 miljon stories
- Hundratals nya stories varje vecka
- Få tillgång till exklusivt innehåll
- Avsluta när du vill
Hands-On Red Team Tactics: A practical guide to mastering Red Team operations
- Språk
- Engelska
- Format
- Kategori
Fakta
Your one-stop guide to learning and implementing Red Team tactics effectively
Key Features
• Target a complex enterprise environment in a Red Team activity
•
• Detect threats and respond to them with a real-world cyber-attack simulation
•
• Explore advanced penetration testing tools and techniques
•
Book Description
Red Teaming is used to enhance security by performing simulated attacks on an organization in order to detect network and system vulnerabilities. Hands-On Red Team Tactics starts with an overview of pentesting and Red Teaming, before giving you an introduction to few of the latest pentesting tools. We will then move on to exploring Metasploit and getting to grips with Armitage. Once you have studied the fundamentals, you will learn how to use Cobalt Strike and how to set up its team server.
The book introduces some common lesser known techniques for pivoting and how to pivot over SSH, before using Cobalt Strike to pivot. This comprehensive guide demonstrates advanced methods of post-exploitation using Cobalt Strike and introduces you to Command and Control (C2) servers and redirectors. All this will help you achieve persistence using beacons and data exfiltration, and will also give you the chance to run through the methodology to use Red Team activity tools such as Empire during a Red Team activity on Active Directory and Domain Controller.
In addition to this, you will explore maintaining persistent access, staying untraceable, and getting reverse connections over different C2 covert channels.
By the end of this book, you will have learned about advanced penetration testing tools, techniques to get reverse shells over encrypted channels, and processes for post-exploitation.
What you will learn
• Get started with red team engagements using lesser-known methods
•
• Explore intermediate and advanced levels of post-exploitation techniques
•
• Get acquainted with all the tools and frameworks included in the Metasploit framework
•
• Discover the art of getting stealthy access to systems via Red Teaming
•
• Understand the concept of redirectors to add further anonymity to your C2
•
• Get to grips with different uncommon techniques for data exfiltration
Who this book is for
Hands-On Red Team Tactics is for you if you are an IT professional, pentester, security consultant, or ethical hacker interested in the IT security domain and wants to go beyond Penetration Testing. Prior knowledge of penetration testing is beneficial.
© 2018 Packt Publishing (E-bok): 9781788997003
Utgivningsdatum
E-bok: 28 september 2018
Taggar
Andra gillade också ...
- The LSAT Law School Admission Test Study Guide Volume I - Reading Comprehension, Logical Reasoning, Writing Sample, and Analytical Reasoning Review Proven Methods for Passing the LSAT Exam With Confidence SMG
- Leadership Two Words at a Time: Simple Truths for Leading Complicated People Bill Treasurer
- Ignite Your Strategy: 7 Steps to Identify What Matters and Build a Winning Future Jules Aubert
- Digital Pilgrims: Towards a Quantum Humanity Adrián Sicilia
- Nattankare Kristina Ohlsson
4.1
- Följeslagaren Sofie Sarenbrant
4
- De som ska dö - Del 1 Christian Frost
2.2
- En dold skönhet Lucinda Riley
4.3
- Vägen in Peter Lindmark
4.4
- Kannibalen Alexandra-Therese Keining
4
- Välkomna till vårt äktenskap Julia Dufvenius
4
- Mörkret faller över skogen Mons Kallentoft
3.6
- Mordet på Henrik Lars Olof Lampers
3.8
- Konstnären Dag Öhrlund
4.1
- Hembiträdet Freida McFadden
4.2
- De fenomenala fruntimren på Grand Hôtel Ruth Kvarnström-Jones
4.5
- Väninnorna på Nordiska Kompaniet Ruth Kvarnström-Jones
4.1
- Tårarnas dal Gustaf Lundskog
4.2
- Jag tycker det är tungt nu Karin Adelsköld
4.5
Därför kommer du älska Storytel:
1 miljon stories
Lyssna och läs offline
Exklusiva nyheter varje vecka
Kids Mode (barnsäker miljö)
Premium
Lyssna och läs ofta.
1 konto
100 timmar/månad
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Unlimited
Lyssna och läs obegränsat.
1 konto
Lyssna obegränsat
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Family
Dela stories med hela familjen.
2-6 konton
100 timmar/månad för varje konto
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
2 konton
239 kr /månadFlex
Lyssna och läs ibland – spara dina olyssnade timmar.
1 konto
20 timmar/månad
Spara upp till 100 olyssnade timmar
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Svenska
Sverige