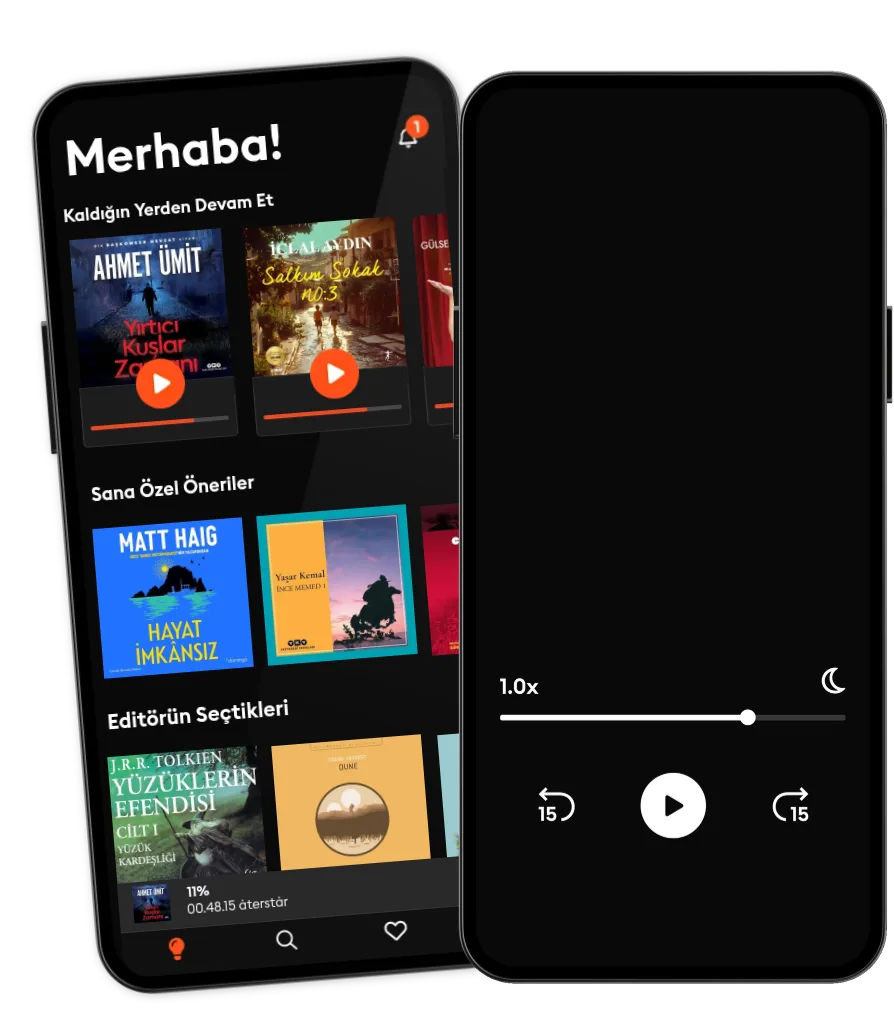
Dinle ya da oku
Sesli kitapların büyülü dünyasına adım at.
- İlk 4 ay ₺124,99/ay
- Binlerce sesli kitap ve e-kitap.
- Dilediğin kadar dinle ya da oku.
- Çevrimdışı modu.
- İstediğin zaman iptal et.
Combatting Cyber Terrorism: A guide to understanding the cyber threat landscape and incident response planning
- Yazan
- Seslendiren:
- Yayınevi
- Süre
- 6Sa 17dk
- Dil
- İngilizce
- Format
- Kategori
Kurgu Dışı
In his second book with IT Governance Publishing, Richard Bingley's Combatting Cyber Terrorism – A guide to understanding the cyber threat landscape and incident response planning analyses the evolution of cyber terrorism and what organisations can do to mitigate this threat. This book discusses:
- Definitions of cyber terrorism; - Ideologies and idealisations that can lead to cyber terrorism; - How threat actors use computer systems to diversify, complicate and increase terrorist attack impacts; - The role of Big Tech and social media organisations such as X (formerly Twitter) and Instagram within the cyber threat landscape; and - How organisations can prepare for acts of cyber terrorism via security planning and incident response strategies such as ISO 31000, ISO 27001 and the NIST Cybersecurity Framework.Increasingly, cyber security practitioners are confronted with a stark phrase: cyber terrorism. For many, it conveys fear and hopelessness. What is this thing called 'cyber terrorism' and what can we begin to do about it? Malicious-minded ICT users, programmers and even programs (including much AI-powered software) have all been instrumental in recruiting, inspiring, training, executing and amplifying acts of terrorism. This has resulted in the loss of life and/or life-changing physical injuries that could never have occurred without support and facilitation from the cyber sphere. These types of attacks can be encapsulated by the phrase 'cyber terrorism'. This book recounts case studies to show the types of threats we face and provides a comprehensive coverage of risk management tactics and strategies to protect yourself against such nefarious threat actors. These include key mitigation and controls for information security or security and HR-related professionals.
© 2024 IT Governance Publishing Ltd (Sesli Kitap): 9781787785229
Yayın tarihi
Sesli Kitap: 25 Ekim 2024
Etiketler
Bunları da beğenebilirsin...
- Plain Talk: Lessons from a Business Maverick Ken Iverson
- Retire Filthy Rich with Real Estate Ravi Sharma
- The Entrepreneurial Mom: Managing for Success in Your Home and Your Business Mary E. Davis
- Unfolded: Lessons in Transformation from an Origami Crane Brian Schubring
- The Social Entrepreneur: The Business of Changing the World
- Cahillik Hakkı Volkan Sönmez
4.5
- Bir Delinin Hatıra Defteri Nikolay Gogol
4.3
- Beş Ses Bir Sır Aslı Aktümen
4.4
- Salkım Sokak No.3 İclal Aydın
4.8
- Hayat İmkânsız Matt Haig
4.3
- Yırtıcı Kuşlar Zamanı Ahmet Ümit
4.7
- Engereğin Gözü Zülfü Livaneli
4.5
- Rezonans Kanunu Pierre Franckh
4.3
- Harry Potter ve Felsefe Taşı J.K. Rowling
4.3
- Gece Yarısı Kütüphanesi Matt Haig
4.6
- İnce Memed 1 Yaşar Kemal
4.9
- Düşüncenin Gücü James Allen
4.1
- Cumhuriyet'in İlk Sabahı İlber Ortaylı
4.9
- Anne Kafamda Bit Var Tarık Akan
4.8
- Mahalleden Arkadaşlar Selçuk Aydemir
4.7
Storytel dünyasını keşfet:
Kids mode
Çevrimdışı modu
İstediğin zaman iptal et
Her yerde erişim
Sınırsız
Sınırsızca dinlemek ve okumak isteyenler için.
₺249.99 /ay
İstediğin zaman iptal et
Sınırsız Yıllık
Sınırsızca dinlemek ve okumak isteyenler için.
₺1499.99 /yıl
İstediğin zaman iptal et
Aile (2 hesap)
Hikayeleri sevdikleri ile paylaşmak isteyenler için.
₺379.99 /ay
İstediğin zaman iptal et
Aile (3 hesap)
Hikayeleri sevdikleri ile paylaşmak isteyenler için.
₺474.99 /ay
İstediğin zaman iptal et
Türkçe
Türkiye