The Complete Metasploit Guide: Explore effective penetration testing techniques with Metasploit
- Höfundur
- Útgefandi
- 1 einkunn
5
- Tungumál
- enska
- Gerð
- Flokkur
Óskáldað efni
Master the Metasploit Framework and become an expert in penetration testing.
Key Features • Gain a thorough understanding of the Metasploit Framework
• Develop the skills to perform penetration testing in complex and highly secure environments
• Learn techniques to integrate Metasploit with the industry’s leading tools
Book Description
Most businesses today are driven by their IT infrastructure, and the tiniest crack in this IT network can bring down the entire business. Metasploit is a pentesting network that can validate your system by performing elaborate penetration tests using the Metasploit Framework to secure your infrastructure.
This Learning Path introduces you to the basic functionalities and applications of Metasploit. Throughout this book, you’ll learn different techniques for programming Metasploit modules to validate services such as databases, fingerprinting, and scanning. You’ll get to grips with post exploitation and write quick scripts to gather information from exploited systems. As you progress, you’ll delve into real-world scenarios where performing penetration tests are a challenge. With the help of these case studies, you’ll explore client-side attacks using Metasploit and a variety of scripts built on the Metasploit Framework.
By the end of this Learning Path, you’ll have the skills required to identify system vulnerabilities by using thorough testing.
This Learning Path includes content from the following Packt products:
• Metasploit for Beginners by Sagar Rahalkar
• Mastering Metasploit - Third Edition by Nipun Jaswal
What you will learn • Develop advanced and sophisticated auxiliary modules
• Port exploits from Perl, Python, and many other programming languages
• Bypass modern protections such as antivirus and IDS with Metasploit
• Script attacks in Armitage using the Cortana scripting language
• Customize Metasploit modules to modify existing exploits
• Explore the steps involved in post-exploitation on Android and mobile platforms
Who this book is for
This Learning Path is ideal for security professionals, web programmers, and pentesters who want to master vulnerability exploitation and get the most of the Metasploit Framework. Basic knowledge of Ruby programming and Cortana scripting language is required.
Sagar Rahalkar is a seasoned information security professional having more than 10 years of comprehensive experience in various verticals of IS. His domain expertise is mainly into breach detection, cyber crime investigations, digital forensics, application security, vulnerability assessment and penetration testing, compliance for mandates and regulations, IT GRC, and much more. He holds a master’s degree in computer science and several industry-recognized certifications such as Certified Cyber Crime Investigator, Certified Ethical Hacker, Certified Security Analyst, ISO 27001 Lead Auditor, IBM certified Specialist-Rational AppScan, Certified Information Security Manager (CISM), and PRINCE2. He has been closely associated with Indian law enforcement agencies for more than 3 years dealing with digital crime investigations and related training and received several awards and appreciations from senior officials of the police and defense organizations in India. Sagar has also been a reviewer and author for various books and online publications. Nipun Jaswal is an international cybersecurity author and an award-winning IT security researcher with a decade of experience in penetration testing, vulnerability assessments, surveillance and monitoring solutions, and RF and wireless hacking. He has authored Metasploit Bootcamp, Mastering Metasploit, and Mastering Metasploit—Second Edition, and co-authored the Metasploit Revealed set of books. He has authored numerous articles and exploits that can be found on popular security databases, such as packet storm and exploit-db. Please feel free to contact him at @nipunjaswal.
© 2019 Packt Publishing (Rafbók): 9781838826901
Útgáfudagur
Rafbók: 25 juni 2019
Aðrir höfðu einnig áhuga á...
- Infrastructure Attack Strategies for Ethical Hacking Himanshu Sharma
- Summary, Analysis, and Review of Martha MacCallum's Unknown Valor: A Story of Family, Courage, and Sacrifice from Pearl Harbor to Iwo Jima Start Publishing Notes
- Summary, Analysis, and Review of Peter Schweizer's Profiles in Corruption: Abuse of Power by America's Progressive Elite Start Publishing Notes
- Modern API Design with gRPC Hitesh Pattanayak
- Sé eftir þér Colleen Hoover
- Hulda Ragnar Jónasson
- Hið ósagða - Ættarsaga Torill Thorup
- Örlagadansinn Birgitta H. Halldórsdóttir
- 18 rauðar rósir Unnur Lilja Aradóttir
- Þögul vitni - Ættarsaga Torill Thorup
- Hildur Satu Rämö
- Lára fer í sund Birgitta Haukdal
- Fjórar árstíðir. Sjálfsævisaga Reynir Finndal Grétarsson
- Jól á Tenerife Sandra Clausen
- Fylgdu fiðrildinu Martta Kaukonen
- Hin helga kvöl Stefán Máni
- Þernan: Undir yfirborðinu Freida McFadden
- Feðgarnir á Fremra-Núpi Ingibjörg Sigurðardóttir
- Prettir í paradís Christina Lauren
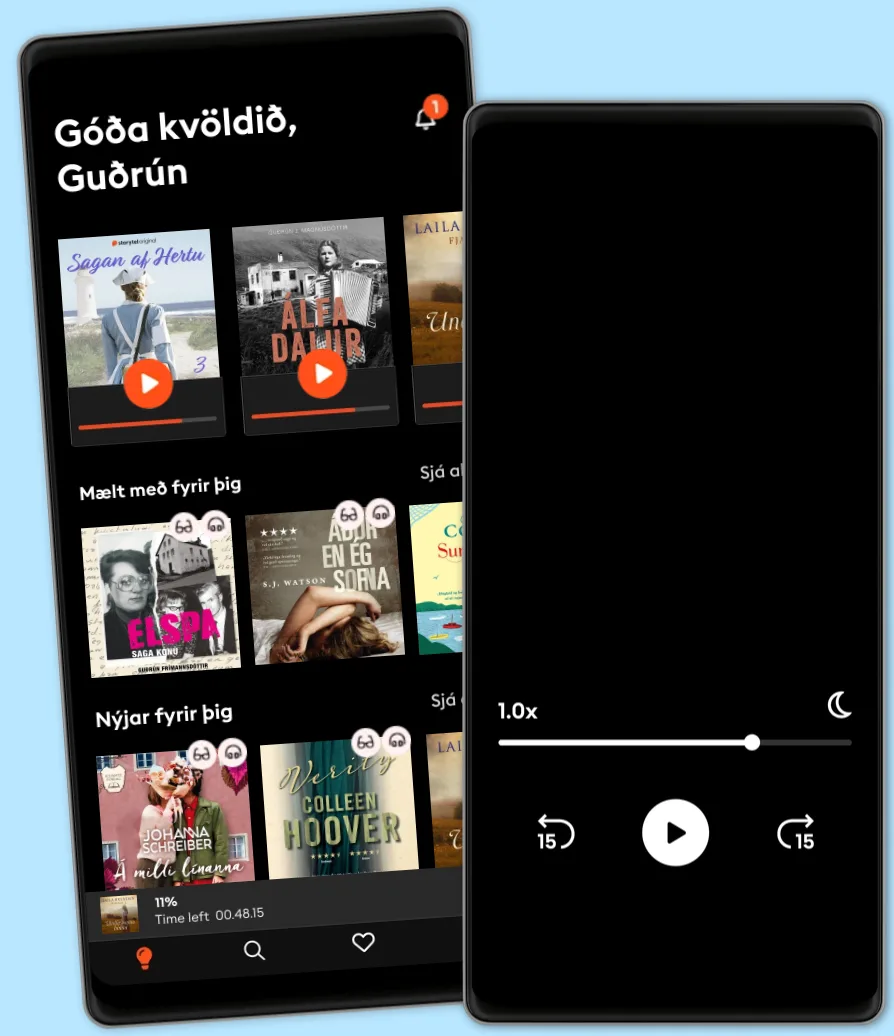
Veldu áskrift
Yfir 900.000 hljóð- og rafbækur
Yfir 400 titlar frá Storytel Original
Barnvænt viðmót með Kids Mode
Vistaðu bækurnar fyrir ferðalögin
Hlustaðu og lestu á sama tíma
Unlimited
Besti valkosturinn fyrir einn notanda
3290 kr /mánuði
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
Family
Fyrir þau sem vilja deila sögum með fjölskyldu og vinum.
Byrjar á 3990 kr /mánuður
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
3990 kr /mánuði