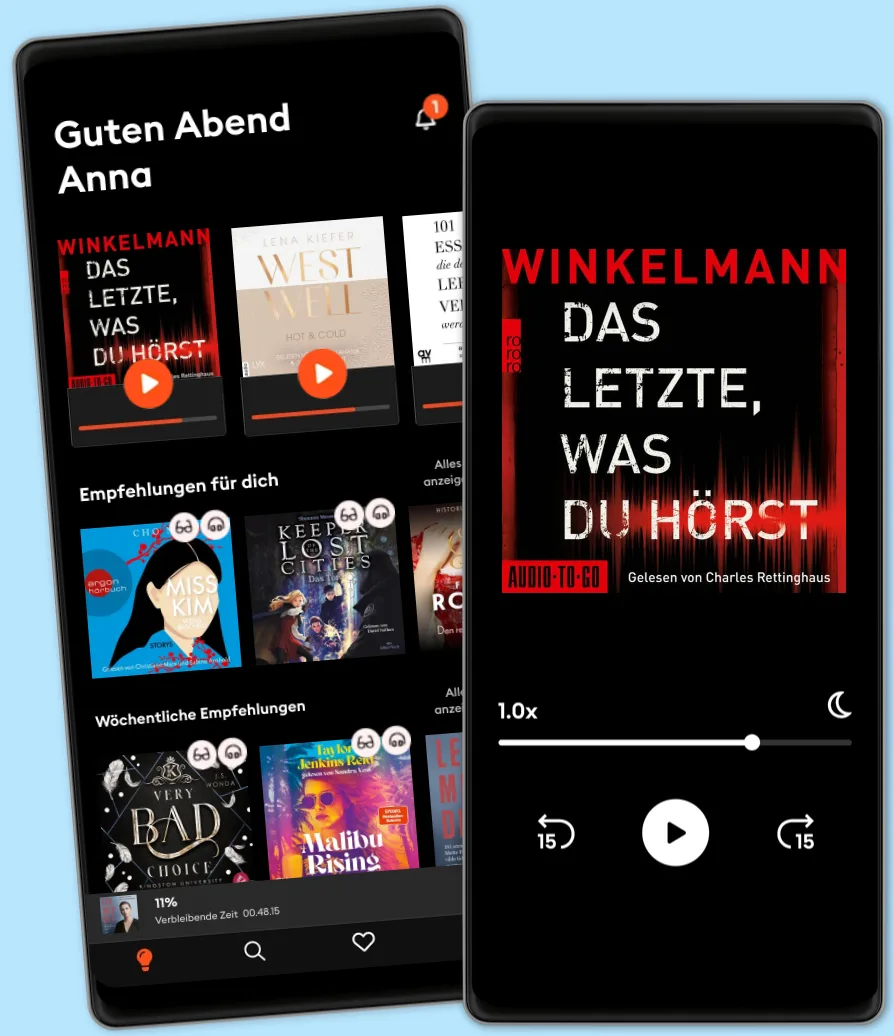
Hören und Lesen
Tritt ein in eine Welt voller Geschichten
- Mehr als 600.000 Hörbücher und E-Book
- Jederzeit kündbar
- Exklusive Titel und Originals
- komfortabler Kinder-Modus
Cybersecurity, Cryptography And Network Security For Beginners: Learn Fast How To Get A Job In Cybersecurity
- Von
- Mit:
- Verlag
2 AUDIOBOOKS IN 1!
• Book 1 - Cryptography Fundamentals & Network Security • Book 2 - How To Get Into Cybersecurity Without Technical Background
You will learn: AUDIOBOOK 1:
What is Confidentiality, Integrity, Availability
•Security Incident Events and Monitoring
•Security Terminologies, Security Zones
•TCP SYN Flood attack, Ping of death attack
•Botnet, IP & MAC Address Spoofing
•DHCP Server & Client Spoofing
•Social Engineering & Phishing
•Spear phishing, Whaling & Pharming
•Watering hole attack & Smishing
•Brute Force & Dictionary Attacks
•Securing and Managing Endpoints
•Securing and Managing Network Devices
•BYOD Security
•Email Security and Blacklisting
•Data Loss Prevention and more
AUDIOBOOK 2: •You will learn the pros and cons of Cybersecurity Jobs, so you can have a better understanding of this industry.
•You will learn a strategy that you use to comprehend the demand for Cybersecurity Professionals within your area.
•You will learn what salary you can expect in the field of Cybersecurity.
•You will learn the differences between security certification and what value each has when you enter this industry.
•You will learn about Cybersecurity skills that you must have before entering this field.
•You will learn ways to think outside the box and quickly adopt a “Cybersecurity Mindset”,
•You will learn how you can get working experience and references while you can also get paid.
•You will learn how to create a Professional LinkedIn Profile step by step that will help you get noticed, and begin socializing with other Cybersecurity Professionals and more…
© 2020 HUGO HOFFMAN (Hörbuch): 9781664934351
Erscheinungsdatum
Hörbuch: 27. November 2020
Tags
Anderen gefällt...
- Cybersecurity Fundamentals: How to Establish Effective Security Management Functions John Knowles
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1 John Knowles
- The Cybersecurity Playbook: How Every Leader and Employee Can Contribute to a Culture of Security Allison Cerra
- Cyber Intelligence Driven Risk: How to Build, Deploy, and Use Cyber Intelligence for Improved Business Risk Decisions Richard O. Moore III
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyond Matt Reyes
- The Doomsday Calculation: How an Equation that Predicts the Future Is Transforming Everything We Know About Life and the Universe William Poundstone
- Cybersecutity First Principles Rick Howard
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business Kim Crawley
- Hacking: How to Hack Alex Wagner
- Haptics Lynette Jones
- Social Capital: Life online in the shadow of Ireland’s tech boom Aoife Barry
- Preventing the Next Pandemic: Vaccine Diplomacy in a Time of Anti-science Peter J. Hotez
- Exposed: How Revealing Your Data and Eliminating Privacy Increases Trust and Liberates Humanity Ben Malisow
- Spatial Computing Pamela Vold
- Web3: Charting the Internet's Next Economic and Cultural Frontier Alex Tapscott
- (ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide 9th Edition Mike Chapple
- Is That a Fact?: Frauds, Quacks, and the Real Science of Everyday Life Dr. Joe Schwarcz
- Cybercrime Investigators Handbook Graeme Edwards
- Counter-Intelligence: What the Secret World Can Teach Us About Problem-solving and Creativity Robert Hannigan
- Quantum Computing For Dummies whurley
- Certified Information Security Manager CISM Study Guide Mike Chapple, PhD, CISM
- What is the Dark Web?: The truth about the hidden part of the internet Evan J. Rodgers
- Accountable: The Rise of Citizen Capitalism Michael O'Leary
- The New Roaring Twenties: Prosper in Volatile Times Paul Zane Pilzer
- Age of Invisible Machines: A Practical Guide to Creating a Hyperautomated Ecosystem of Intelligent Digital Workers Robb Wilson
- How Big-Tech Barons Smash Innovation—and How to Strike Back Maurice E. Stucke
- Ethical Machines: Your Concise Guide to Totally Unbiased, Transparent, and Respectful AI Reid Blackman
- Human Work in the Age of Smart Machines Jamie Merisotis
- The Blue Revolution: Hunting, Harvesting, and Farming Seafood in the Information Age Nicholas Sullivan
- Waves Fredric Raichlen
- The Legal Analyst: A Toolkit for Thinking about the Law Ward Farnsworth
- Cybersecurity For Dummies Joseph Steinberg
- The Information Trade: How Big Tech Conquers Countries, Challenges Our Rights, and Disrupts Our World: How Big Tech Conquers Countries, Challenges Our Rights, and Transforms Our World Alexis Wichowski
- New Laws of Robotics: Defending Human Expertise in the Age of AI Frank Pasquale
- A History of Video Games in 64 Objects World Video Game Hall of Fame
- Ethical Hacking With Kali Linux: Learn Fast How To Penetrate Wired Or Wireless Networks | 2 Books In 1 HUGO HOFFMAN
- The Vanishing American Corporation: Navigating the Hazards of a New Economy Gerald F. Davis
- Ever Wonder Why?: And Other Controversial Essays Thomas Sowell
- CompTIA Security+ All-in-One Exam Guide, Sixth Edition (Exam SY0-601) Wm. Arthur Conklin
- Exploding Data: Reclaiming Our Cyber Security in the Digital Age Michael Chertoff
- The Space Economy: Capitalize on the Greatest Business Opportunity of Our Lifetime Chad Anderson
- Genentech: The Beginnings of Biotech Sally Smith Hughes
- Maxims for Thinking Analytically: The Wisdom of Legendary Harvard Professor Richard Zeckhauser Dan Levy
- CISSP Exam Study Guide For Cybersecurity Professionals: 2 Books In 1: Beginners Guide To Nist Cybersecurity Framework & Risk Management Governance Strategies HUGO HOFFMAN
- 3D Printing John M. Jordan
- Trustworthy AI: A Business Guide for Navigating Trust and Ethics in AI Beena Ammanath
- The Great Reversal: How America Gave Up on Free Markets Thomas Philippon
- How Rights Went Wrong: Why Our Obsession with Rights Is Tearing America Apart Jamal Greene
- The Aisles Have Eyes: How Retailers Track Your Shopping, Strip Your Privacy, and Define Your Power Joseph Turow
- CRISPR People: The Science and Ethics of Editing Humans Henry T. Greely
- Greedy Bastards: Corporate Communists, Banksters, and the Other Vampires Who Suck America Dry Dylan Ratigan
- In the Year of the Tiger: Why it's not too late to learn from China Dr. Angelika Berger-Sodian
- Billionaires in World Politics Peter Hagel
- The Art of Attack: Attacker Mindset for Security Professionals Maxie Reynolds
- Quantum Physics Made Easy: The Introduction Guide For Beginners Who Flunked Maths And Science In Plain Simple English Donald B. Grey
- The Billion Dollar Molecule: One Company's Quest for the Perfect Drug Barry Werth
- How to Measure Anything in Cybersecurity Risk, 2nd Edition Douglas W. Hubbard
- The Illusion of Control: Why Financial Crises Happen, and What We Can (and Can't) Do About It Jon Danielsson
- Distrust: Big Data, Data-Torturing, and the Assault on Science Gary Smith
- Software Development Fundamentals Introbooks Team
- Trading at the Speed of Light: How Ultrafast Algorithms Are Transforming Financial Markets Donald MacKenzie
- Seven Games: A Human History Oliver Roeder
- Building a Cyber Risk Management Program: Evolving Security for the Digital Age Brian Allen
- Cyber Mayday and the Day After: A Leader's Guide to Preparing, Managing, and Recovering from Inevitable Business Disruptions Daniel Lohrmann
- Hackable: How to Do Application Security Right Ted Harrington
- Virtual Reality Samuel Greengard
- Behavioural Economics: Psychology, neuroscience, and the human side of economics David Orrell
- Thinking Like an Economist: How Efficiency Replaced Equality in U.S. Public Policy Elizabeth Popp Berman
- A Leader’s Guide to Cybersecurity: Why Boards Need to Lead-And How to Do It Jack J. Domet
- CISSP And Cybersecurity For Beginners: Penetration Testing And Ethical Hacking Techniques To Defend Your Infrastructure 3 Books In 1 John Knowles
- The Road to Reinvention: How to Drive Disruption and Accelerate Transformation Josh Linkner
- Isaac Newton: A Biography of an Inventor, Astronomer, Physicist, and Philosopher Mitch Stokes
- The Cyber-Elephant In The Boardroom: Cyber-Accountability With The Five Pillars Of Security Framework Mathieu Gorge
- Deep Learning: Guide to Machine Learning and Artificial Intelligence David Feldspar
- The End of Cheap China: Economic and Cultural Trends That Will Disrupt the World Shaun Rein
- The Dictatorship of Woke Capital: How Political Correctness Captured Big Business Stephen R. Soukup
- The Knowledge Gene Lynne Kelly
- Fake Photos Hany Farid
- Understandable Economics: Because Understanding Our Economy Is Easier Than You Think and More Important Than You Know Howard Yaruss
- The Rise and Decline of Nations: Economic Growth, Stagflation, and Social Rigidities Mancur Olson
- Imitation Democracy: The Development of Russia's Post-Soviet Political System Dmitrii Furman
- Flesh Made New: The Unnatural History and Broken Promise of Stem Cells John Rasko
- Hacking the Hacker: Learn From the Experts Who Take Down Hackers Roger A. Grimes
- Fourth Wing – Flammengeküsst (Flammengeküsst-Reihe 1) Rebecca Yarros
4.7
- Iron Flame – Flammengeküsst (Flammengeküsst-Reihe 2): Die heißersehnte Fortsetzung des Fantasy-Erfolgs »Fourth Wing« Rebecca Yarros
4.7
- Onyx Storm – Flammengeküsst (Flammengeküsst-Reihe 3): Die heißersehnte Fortsetzung von »Fourth Wing« und »Iron Flame« Rebecca Yarros
4.3
- Just for the Summer Abby Jimenez
4.5
- House of Verity: Zeit tötet immer Marah Woolf
4.7
- The Wind Weaver (The Wind Weaver 1): Sturmverführt | Der Auftakt der fantastischen Romantasy-Trilogie Julie Johnson
4.4
- Anymore - Dunbridge Academy, Teil 4 (Ungekürzt) Sarah Sprinz
4
- Rubinrot - Liebe geht durch alle Zeiten - Liebe geht durch alle Zeiten. Die Edelstein-Trilogie, Band 1 (Ungekürzte Lesung) Kerstin Gier
4.7
- Das Familienfest - Ein packender Psychothriller voll unvorhersehbarer Twists (Ungekürzt) B.P. Walter
3.4
- "Mama, bitte lern Deutsch" - Unser Eingliederungsversuch in eine geschlossene Gesellschaft (Ungekürzte Autorenlesung) Tahsim Durgun
4.8
- Der dunkle Sommer (Ungekürzte Lesung) Vera Buck
4.7
- Not Quite Dead Yet (Ungekürzt) Holly Jackson
4.5
- Throne of Glass 1: Die Erwählte Sarah J. Maas
4.6
- Hopeless - Chestnut Springs, Teil 5 (Ungekürzt) Elsie Silver
4.5
- Throne of Glass 2: Kriegerin im Schatten Sarah J. Maas
4.7
Wähle dein Abo-Modell
Über 600.000 Titel
Lade Titel herunter mit dem Offline Modus
Exklusive Titel und Storytel Originals
Sicher für Kinder (Kindermodus)
Einfach jederzeit kündbar
Unlimited
Für alle, die unbegrenzt hören und lesen möchten.
1 Konto
Unbegrenzter Zugriff
Jederzeit kündbar
Wechsel zu Basic jederzeit möglich
Basic
Für alle, die gelegentlich hören und lesen.
1 Konto
20 Stunden/pro Monat
Jederzeit kündbar
Abo-Upgrade jederzeit möglich
Deutsch
Deutschland