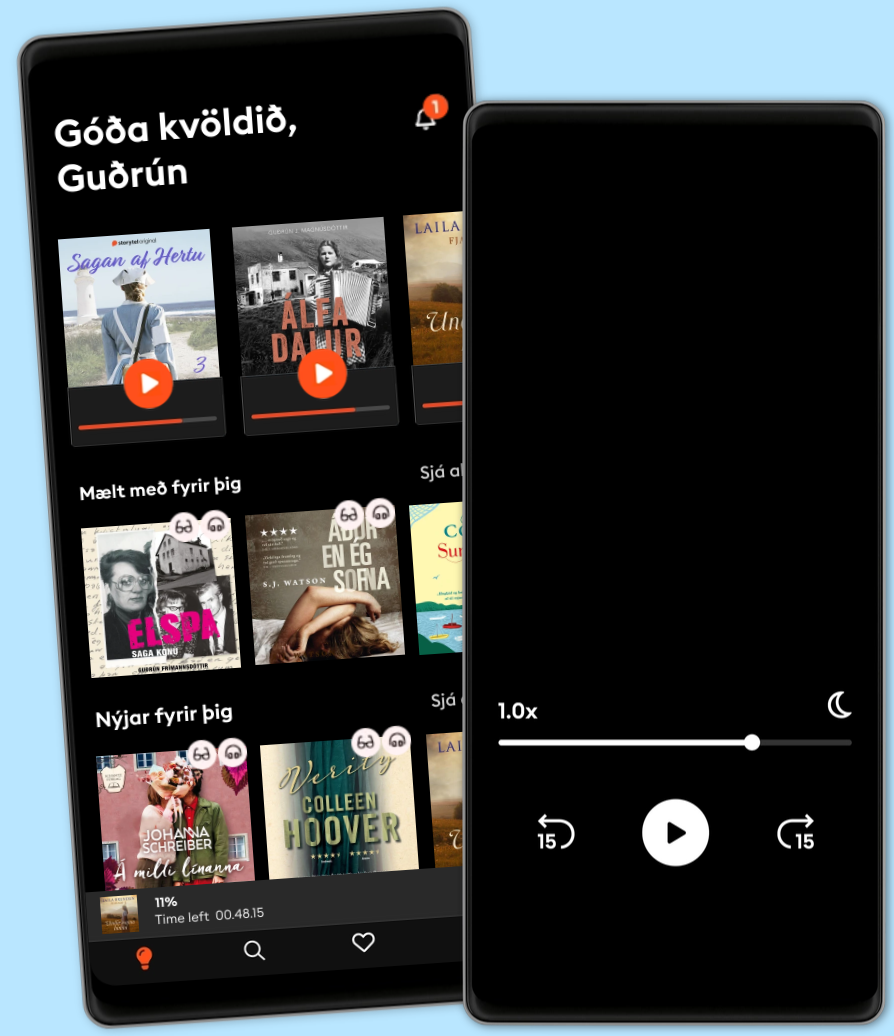
Hlustaðu og lestu
Stígðu inn í heim af óteljandi sögum
- Lestu og hlustaðu eins mikið og þú vilt
- Þúsundir titla
- Getur sagt upp hvenær sem er
- Engin skuldbinding
Metasploit Techniques and Workflows: Definitive Reference for Developers and Engineers
- Höfundur
- Útgefandi
- Tungumál
- enska
- Format
- Flokkur
Óskáldað efni
"Metasploit Techniques and Workflows"
"Metasploit Techniques and Workflows" is an advanced, comprehensive guide to mastering the Metasploit Framework, designed for experienced penetration testers, red teamers, and security engineers seeking to elevate their offensive security capabilities. The book begins with an in-depth exploration of Metasploit’s modular internals, revealing its architecture, core libraries, module APIs, and database integration. Readers gain hands-on insight into extending Metasploit through custom code, developing plugins, and maintaining compatibility across evolving versions—laying a technical foundation crucial for effective real-world engagements.
Building upon this expertise, the text meticulously covers each phase of the attack lifecycle. Reconnaissance workflows blend Metasploit with industry-standard tools for advanced scanning, fingerprinting, and vulnerability automation. Detailed exploitation chapters provide actionable strategies for module selection, payload management, and bypassing modern defensive mechanisms such as DEP, ASLR, and endpoint protections. Readers are equipped to engineer bespoke exploits and payloads for cross-platform operations, while post-exploitation guidance addresses privilege escalation, persistence, lateral movement, data exfiltration, and anti-forensics techniques. Rich case studies and adversary simulation frameworks ensure practical, adversary-informed understanding.
The later chapters propel professionals toward automation and large-scale operations, detailing advanced scripting, API integrations, and CI/CD pipeline utilization. Metasploit’s role in coordinated red team, purple team, and adversary simulation exercises is examined, complemented by robust coverage of detection, response, and defensive countermeasures. Forward-looking insights analyze AI augmentation, cloud and IoT exploitation trends, and evolving ethical considerations, solidifying this work as an essential reference for those driving offensive security innovation and resilience.
© 2025 HiTeX Press (Rafbók): 6610000807840
Útgáfudagur
Rafbók: 24 maj 2025
Merki
- Dauðinn einn var vitni Stefán Máni
4.4
- Út við svala sjávarströnd Birgitta H. Halldórsdóttir
4
- Opinberanir Torill Thorup
4.3
- 17 ástæður til að drepa Unnur Lilja Aradóttir
4
- Þar sem hjartað slær Birgitta H. Halldórsdóttir
4.2
- Ég er ekki dáinn Erik Engelv
3.8
- Ástríðan í fjöllunum Karin Härjegård
4.2
- Lára missir tönn Birgitta Haukdal
4.6
- Ég ætla að djamma þar til ég drepst Ívar Örn Katrínarson
4.4
- Hann átti mig: Sönn saga um það að komast lifandi frá ofbeldismanni Leone Milton
4.3
- Heim fyrir myrkur Eva Björg Ægisdóttir
4.2
- Völundur Steindór Ívarsson
4.3
- Vigdís - Kona verður forseti Páll Valsson
4.6
- Lykillinn Kathryn Hughes
4.4
- Tvöfalt líf kærastans: Sönn saga Cleo James
3.8
Veldu áskrift
Yfir 900.000 hljóð- og rafbækur
Yfir 400 titlar frá Storytel Original
Barnvænt viðmót með Kids Mode
Vistaðu bækurnar fyrir ferðalögin
Unlimited
Besti valkosturinn fyrir einn notanda
1 aðgangur
Ótakmörkuð hlustun
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
Family
Fyrir þau sem vilja deila sögum með fjölskyldu og vinum.
2-6 aðgangar
100 klst/mán fyrir hvern aðgang
Yfir 900.000 hljóð- og rafbækur
Engin skuldbinding
Getur sagt upp hvenær sem er
2 aðgangar
3990 kr /á mánuðiÍslenska
Ísland